Arcitura Education S90.20 Dumps - Pass SOA Security Lab Exam in 2026
The Arcitura Education S90.20 - SOA Security Lab exam is part of the Certified SOA Security Specialist certification path. It is designed for candidates who want to prove their knowledge of securing services, microservices, and SOA environments. This exam matters for professionals who need a strong understanding of both security concepts and practical lab-based application. It helps validate the skills needed to work with modern service architectures in real-world security scenarios.
Exam Topics and Approximate Weightage
| # | Exam Topics | Sub-Topics | Approximate Weightage (%) |
|---|---|---|---|
| 1 | Fundamental SOA, Services & Microservices | SOA principles, service orientation, microservices basics, service interaction models | 18% |
| 2 | Microservice Technology Concepts | Container concepts, deployment patterns, service communication, scalability considerations | 18% |
| 3 | Fundamental Security for Services, Microservices & SOA | Authentication basics, authorization basics, message protection, identity and access concepts | 20% |
| 4 | Advanced Security for Services, Microservices & SOA | Security design strategies, policy enforcement, secure communication, advanced protection controls | 22% |
| 5 | Security Lab for Services, Microservices & SOA | Lab-based scenario analysis, security configuration, problem solving, practical validation of controls | 22% |
The exam tests more than memorization. Candidates must understand core concepts, recognize how security applies across services and microservices, and handle practical lab-style scenarios with confidence. It also checks whether you can apply knowledge to realistic situations, making hands-on understanding and careful exam preparation important.
How QA4Exam.com Helps You Pass
QA4Exam.com offers Exam PDF and Online Practice Test materials that are built to help you prepare efficiently for the Arcitura Education S90.20 exam. The PDF gives you actual questions and answers in a convenient study format, while the practice test helps you experience a real exam simulation.
Using verified answers and up-to-date questions, you can focus on the most relevant exam areas and avoid wasting time on guesswork. The online practice test is especially useful for time management practice, helping you get comfortable with the exam pace before test day.
With both formats combined, you can study smarter, strengthen weak areas, and improve your chances of passing on the first attempt.
Frequently Asked Questions
1. Who should take the Arcitura Education S90.20 SOA Security Lab exam?
This exam is for candidates pursuing the Certified SOA Security Specialist certification and for professionals who want to validate their knowledge of securing services, microservices, and SOA environments.
2. Is the SOA Security Lab exam difficult?
It can be challenging because it covers both concepts and practical security application. Candidates who understand the topics and practice with realistic questions usually feel more prepared.
3. Can I pass with only braindumps?
Relying on dumps alone is not a smart strategy. You should use them as a study aid alongside topic review and practice so you understand the exam instead of just memorizing answers.
4. Do I need hands-on experience for this exam?
Hands-on understanding is very helpful because the exam includes lab-oriented security topics. Practical familiarity with service and microservice security can improve your confidence and performance.
5. Are the QA4Exam.com dumps and practice test enough to prepare?
They are very useful study tools because they provide actual questions and answers, verified content, and exam simulation. For best results, use them with topic review so you cover both knowledge and test strategy.
6. How do QA4Exam.com dumps help with first-attempt success?
They help you focus on likely exam areas, understand question style, and practice answering under time pressure. That combination can improve readiness and increase your chances of passing on the first attempt.
7. What format do the QA4Exam.com study materials come in?
QA4Exam.com provides an Exam PDF and an Online Practice Test. The PDF is convenient for focused study, while the practice test is designed to simulate the real exam environment.
The questions for S90.20 were last updated on Jun 4, 2026.
- Viewing page 1 out of 6 pages.
- Viewing questions 1-5 out of 30 questions
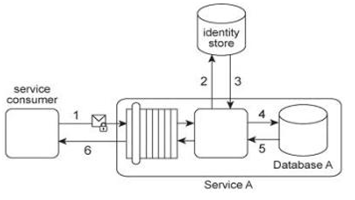
Service A provides a data access capability that can be used by a variety of service consumers. The database records accessed by Service A are classified as either private or public. There are two types of service consumers that use Service A:
Service consumers with public access permissions (allowed to access only public data records) and service consumers with private access permissions (allowed to access all data records). For performance reasons the Service A architecture uses a single database, named Database A .Each record in Database A is classified as either private or public. After Service A is invoked by a service consumer (1), it authenticates the request message using an identity store and retrieves the corresponding authorization (2, 3). Once authorized, the service consumer's request is submitted to Database A (4), which then returns the requested data (5) If the service consumer has private access permissions, all of the returned data is included in Service A's response message (6). If the service consumer has public access permissions, then Service A first filters the data in order to remove all unauthorized private data records before sending to the response message to the service consumer (6). In addition to retrieving data, Service A's data access capability can be used to update database records. An investigation recently revealed an information leakage problem that can occur when service consumers with public access permissions attempt to update the ID value of a database record The ID values of all database records (private or public) must be unique. When a service consumer with public access permissions updates a public database record with an ID value that is already assigned to a private database record, the database returns an error message describing this conflict. This error text reveals confidential information by stating that the ID value submitted by the service consumer with public access permissions already exists within a private database record. What steps can be taken to avoid this problem while preserving the requirement that all database records (private and public) have unique ID values?
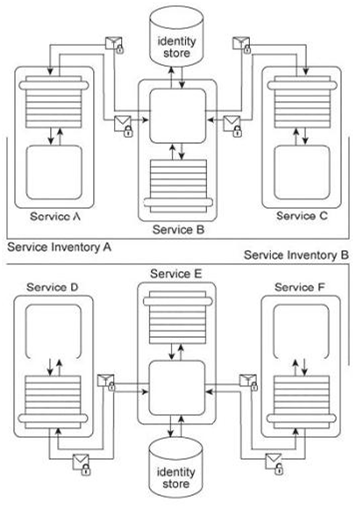
Services A, B, and C reside in Service Inventory A and Services D, E, and F reside in Service Inventory B .Service B is an authentication broker that issues WS-Trust based SAML tokens to Services A and C upon receiving security credentials from Services A and C .Service E is an authentication broker that issues WS-Trust based SAML tokens to Services D and F upon receiving security credentials from Services D and E .Service B uses the Service Inventory A identify store to validate the security credentials of Services A and C .Service E uses the Service Inventory B identity store to validate the security credentials of Services D and F .It is decided to use Service E as the sole authentication broker for all services in Service Inventories A and B .Service B is kept as a secondary authentication broker for load balancing purposes. Specifically, it is to be used for situations where authentication requests are expected to be extra time consuming in order to limit the performance burden on Service E .Even though Service B has all the necessary functionality to fulfill this new responsibility, only Service E can issue SAML tokens to other services. How can these architectures be modified to support these new requirements?
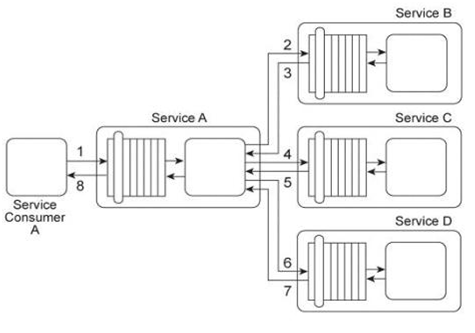
Service A provides a data retrieval capability that can be used by a range of service consumers, including Service Consumer A, In order to retrieve the necessary data. Service Consumer A first sends a request message to Service A (1). Service A then exchanges request and response messages with Service B (2, 3). Service C (4, 5), and Service D (6. 7). After receiving all three response messages from Services B .C .and D, Service A assembles the collected data into a response message that it returns to Service Consumer A (8). The Service A data retrieval capability has been suffering from poor performance, which has reduced its usefulness to Service Consumer A .Upon studying the service composition architecture, it is determined that the performance problem can be partially attributed to redundant validation by service contracts for compliance to security policies. Services B and C have service contracts that contain the same two security policies. And, Service D has a service contract that contains a security policy that is also part of Service A's service contract. What changes can be made to the service contracts in order to improve the performance of the service composition while preserving the security policy compliance requirements?
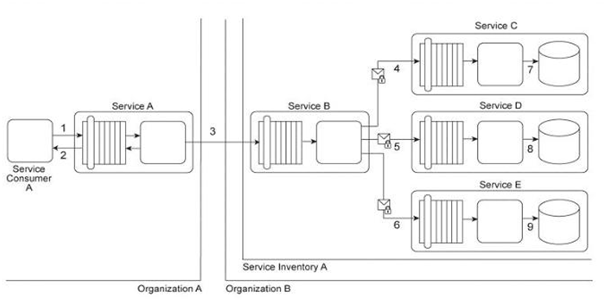
Service Consumer A sends a request to Service A (1). Service A replies with an acknowledgement message (2) and then processes the request and sends a request message to Service B (3). This message contains confidential financial data. Service B sends three different request messages together with its security credentials to Services C, D, and E (4, 5, 6). Upon successful authentication, Services C, D, and E store the data from the message in separate databases (7, 8, 9) Services B, C, D, and E belong to Service Inventory A, which further belongs to Organization B .Service Consumer A and Service A belong to Organization A .The service contracts of Services A and B both comply with the same XML schema. However, each organization employs different security technologies for their service architectures. To protect the confidential financial data sent by Service A to Service B, each organization decides to independently apply the Data Confidentiality and the Data Origin Authentication patterns to establish message-layer security for external message exchanges. However, when an encrypted and digitally signed test message is sent by Service A to Service B, Service B was unable to decrypt the message. Which of the following statements describes a solution that solves this problem?
Service A exchanges messages with Service B multiple times during the same runtime service activity. Communication between Services A and B has been secured using transport-layer security. With each service request message sent to Service B (1A .IB), Service A includes an X.509 certificate, signed by an external Certificate Authority (CA). Service B validates the certificate by retrieving the public key of the CA (2A .2B) and verifying the digital signature of the X.509 certificate. Service B then performs a certificate revocation check against a separate external CA repository (3A, 3B). No intermediary service agents reside between Service A and Service B .
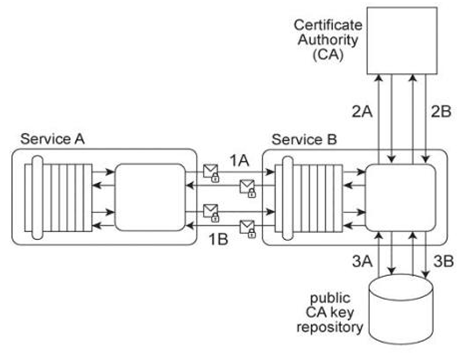
To fulfill a new security requirement, Service A needs to be able to verify that the response message sent by Service B has not been modified during transit. Secondly, the runtime performance between Services A and B has been unacceptably poor and therefore must be improved without losing the ability to verify Service A's security credentials. It has been determined that the latency is being caused by redundant security processing carried out by Service B .Which of the following statements describes a solution that fulfills these requirements?
Unlock All Questions for Arcitura Education S90.20 Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 30 Questions & Answers