Most Recent CompTIA CAS-004 Exam Dumps
Prepare for the CompTIA Advanced Security Practitioner (CASP+) Exam exam with our extensive collection of questions and answers. These practice Q&A are updated according to the latest syllabus, providing you with the tools needed to review and test your knowledge.
QA4Exam focus on the latest syllabus and exam objectives, our practice Q&A are designed to help you identify key topics and solidify your understanding. By focusing on the core curriculum, These Questions & Answers helps you cover all the essential topics, ensuring you're well-prepared for every section of the exam. Each question comes with a detailed explanation, offering valuable insights and helping you to learn from your mistakes. Whether you're looking to assess your progress or dive deeper into complex topics, our updated Q&A will provide the support you need to confidently approach the CompTIA CAS-004 exam and achieve success.
The questions for CAS-004 were last updated on Jun 6, 2026.
- Viewing page 1 out of 122 pages.
- Viewing questions 1-5 out of 611 questions
Which of the following is required for an organization to meet the ISO 27018 standard?
A network architect is designing a new SD-WAN architecture to connect all local sites to a central hub site. The hub is then responsible for redirecting traffic to public cloud and datacenter applications. The SD-WAN routers are managed through a SaaS, and the same security policy is applied to staff whether working in the office or at a remote location. The main requirements are the following:
1. The network supports core applications that have 99.99% uptime.
2. Configuration updates to the SD-WAN routers can only be initiated from the management service.
3. Documents downloaded from websites must be scanned for malware.
Which of the following solutions should the network architect implement to meet the requirements?
A security engineer is re-architecting a network environment that provides regional electric distribution services. During a pretransition baseline assessment, the engineer identified the following security-relevant characteristics of the environment:
* Enterprise IT servers and supervisory industrial systems share the same subnet.
* Supervisory controllers use the 750MHz band to direct a portion of fielded PLCs.
* Command and telemetry messages from industrial control systems are unencrypted and unauthenticated.
Which of the following re-architecture approaches would be best to reduce the company's risk?
The best approach to reduce the company's risk is to segregate the enterprise IT servers and supervisory industrial systems. Creating a new network segment and using a Next-Generation Firewall (NGFW) to enforce a strict segmentation policy will help to isolate the systems and protect against potential attacks. Additionally, implementing a Wireless Intrusion Detection System (WIDS) can help monitor the spectrum for unauthorized devices or interference.
A company is experiencing a large number of attempted network-based attacks against its online store. To determine the best course of action, a security analyst reviews the following logs.
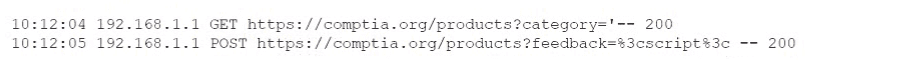
Which of the following should the company do next to mitigate the risk of a compromise from these attacks?
Restricting HTTP methods can mitigate the risk of network-based attacks against an online store by limiting the types of HTTP requests that the server will accept, thus reducing the attack surface. This is a common method to prevent web-based attacks such as Cross-Site Scripting (XSS) and SQL Injection.
A security architect is implementing a SOAR solution in an organization's cloud production environment to support detection capabilities. Which of the following will be the most likely benefit?
SOAR solutions (Security Orchestration, Automation, and Response) are designed to help organizations efficiently manage security operations. They can automate the collection and analysis of security data, which improves the performance of a security operations center (SOC) by allowing the security team to focus on more strategic tasks and reduce response times to incidents.
Unlock All Questions for CompTIA CAS-004 Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 611 Questions & Answers