CrowdStrike IDP Dumps - Pass CrowdStrike Certified Identity Specialist Exam in First Attempt 2026
The CrowdStrike IDP exam is part of the CrowdStrike Certified Identity Specialist certification and is designed for professionals working with identity protection and modern security operations. It validates your understanding of identity-focused security concepts, risk assessment, configuration, and investigation workflows in the CrowdStrike environment. This certification matters for candidates who want to strengthen their skills in identity protection and show practical knowledge of CrowdStrike identity security capabilities.
| # | Exam Topics | Sub-Topics | Approximate Weightage (%) |
|---|---|---|---|
| 1 | Zero Trust Architecture | Trust verification, access control principles, identity-centric security | 8% |
| 2 | Identity Protection Tenets | Protection goals, identity risk concepts, security best practices | 8% |
| 3 | Falcon Identity Protection Fundamentals | Platform overview, core capabilities, detection and visibility basics | 10% |
| 4 | Domain Security Assessment | Domain risk review, exposure indicators, assessment outputs | 8% |
| 5 | Risk Assessment | Risk scoring, prioritization, threat impact analysis | 10% |
| 6 | User Assessment | User behavior review, account risk signals, suspicious activity analysis | 8% |
| 7 | Threat Hunting and Investigation | Investigation workflow, hunting approach, alert analysis | 12% |
| 8 | Risk Management with Policy Rules | Policy creation, rule tuning, response actions | 10% |
| 9 | Configuration and Connectors | Integration setup, data connectors, environment configuration | 8% |
| 10 | Multifactor Authentication (MFA) and Identity-as-a-service (IDaaS) Configuration Basics | MFA concepts, IDaaS fundamentals, authentication setup basics | 8% |
| 11 | Falcon Fusion SOAR for Identity Protection | Automation workflows, orchestration use cases, response actions | 10% |
| 12 | GraphQL API | Query basics, data retrieval, API use for identity operations | 10% |
| Total | 100% | ||
The CrowdStrike IDP exam tests both conceptual understanding and practical application across identity protection, assessment, investigation, and automation tasks. Candidates should be ready to interpret security scenarios, apply policy and configuration knowledge, and understand how CrowdStrike identity protection features work together in real environments.
How QA4Exam.com Helps You Pass
QA4Exam.com provides the CrowdStrike IDP Exam PDF with actual questions and answers, giving you a focused way to review the exam-style content before test day. The Online Practice Test helps you experience a real exam simulation so you can understand the question format, pacing, and difficulty level. With up-to-date questions and verified answers, you can study with more confidence and avoid wasting time on outdated material. The practice test also helps you improve time management so you can stay calm and complete the exam efficiently. Together, these tools make it easier to prepare effectively and aim for a first-attempt pass.
FAQ
What is the CrowdStrike IDP exam?
The CrowdStrike IDP exam is the CrowdStrike Certified Identity Specialist exam focused on identity protection, assessment, investigation, configuration, and automation topics.
Who should take the CrowdStrike Certified Identity Specialist exam?
It is intended for candidates who want to demonstrate knowledge of CrowdStrike identity protection concepts and practical skills related to identity security operations.
Is the CrowdStrike IDP exam difficult?
The exam can be challenging because it covers multiple identity security areas, including risk assessment, investigations, policy rules, and API knowledge.
Can I pass with only braindumps?
Braindumps alone are not the best approach. You should use them with practice and review so you understand the concepts and can answer scenario-based questions confidently.
Do I need hands-on experience for the CrowdStrike IDP exam?
Hands-on experience is helpful because the exam includes practical topics such as configuration, connectors, investigations, and automation workflows.
Are QA4Exam.com dumps enough, or do I need other resources too?
QA4Exam.com dumps and the online practice test are strong study tools, and many candidates also review the official exam topics to strengthen understanding of the subject areas.
How do QA4Exam.com dumps and practice tests help with first-attempt success?
They help you practice real exam-style questions, verify answers, and improve timing so you can study more efficiently and enter the exam with better confidence.
What format do the QA4Exam.com materials come in?
QA4Exam.com offers an Exam PDF with questions and answers plus an Online Practice Test designed to simulate the exam experience.
The questions for IDP were last updated on Jun 2, 2026.
- Viewing page 1 out of 12 pages.
- Viewing questions 1-5 out of 58 questions
When creating an API client, which scope with Write permissions must be enabled prior to using Identity Protection API?
To interact with Falcon Identity Protection using GraphQL, the API client must be created with the appropriate permission scopes. According to the CCIS curriculum, the Identity Protection GraphQL scope with Write permissions must be enabled prior to using the Identity Protection API.
This scope allows the API client to execute GraphQL queries and mutations related to identity detections, incidents, users, and risk data. Even when performing read-only operations, CrowdStrike requires the GraphQL Write scope to authorize GraphQL query execution within the Falcon platform.
The other options are incorrect because:
Identity Protection Assessment and Health are read-only data scopes.
The statement that Write permissions are not required is explicitly false per CCIS documentation.
Because GraphQL access requires the Identity Protection GraphQL (Write) scope, Option D is the correct and verified answer.
Where would a Falcon administrator enable authentication traffic inspection (ATI) for Domain Controllers?
Authentication Traffic Inspection (ATI) is a foundational capability of Falcon Identity Protection that enables the platform to analyze authentication traffic from domain controllers. According to the CCIS documentation, ATI is enabled through Identity configuration policies.
Identity configuration policies define how the Falcon sensor captures and inspects authentication-related traffic, including Kerberos, NTLM, LDAP, and other identity protocols. Enabling ATI at this level ensures that domain controllers provide the necessary telemetry for identity risk analysis, detections, and behavioral profiling.
The other options are incorrect because:
Identity management settings focus on identity governance and administration.
Identity detection configuration controls detection logic, not traffic inspection.
Identity protection settings manage high-level configuration but do not directly enable ATI.
Because ATI must be explicitly enabled via Identity configuration policies, Option A is the correct and verified answer.
Refer to exhibit.
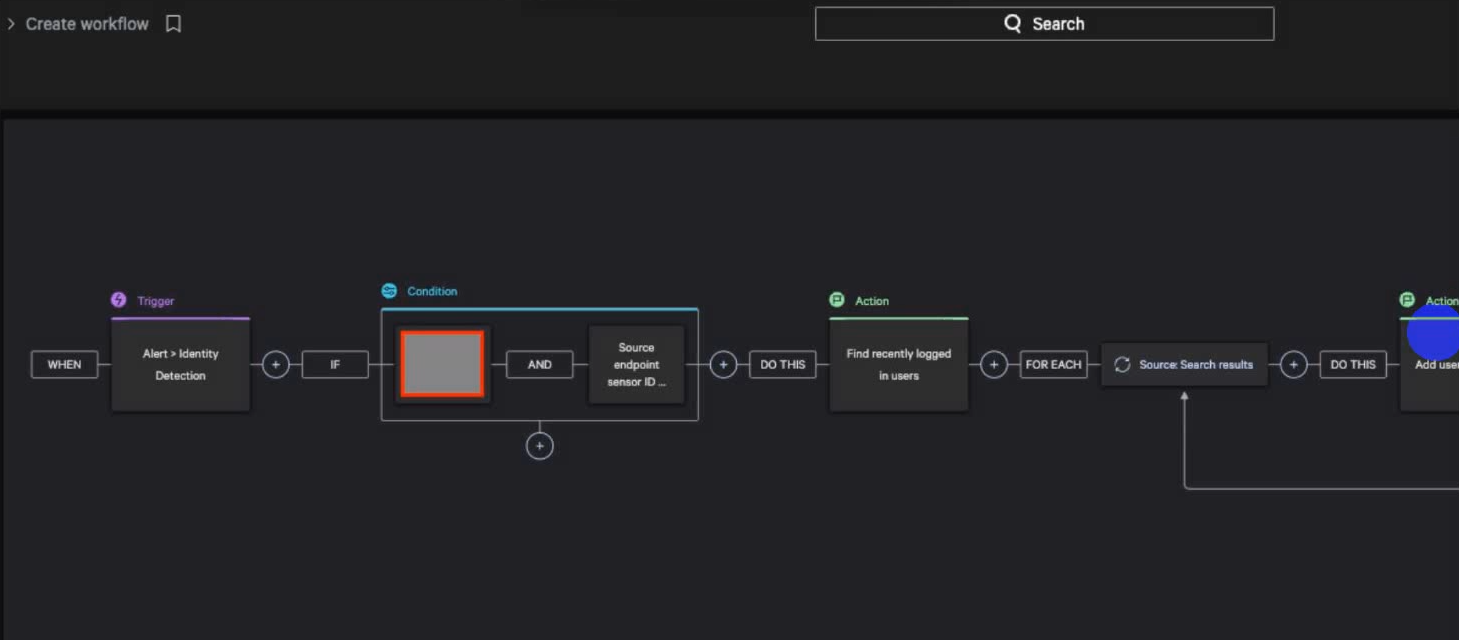
Considering the following example, what MITRE ATT&CK tactic would you use to complete the workflow?
The provided Falcon Fusion SOAR workflow example shows a trigger based on an Identity Detection, followed by conditions and actions that search for recently logged-in users and related entities across endpoints. According to the CCIS curriculum, this type of workflow aligns with the Lateral Movement tactic in the MITRE ATT&CK framework.
Lateral Movement involves an attacker moving from one system or account to another after initial access has been achieved. The workflow's logic---correlating identity detections with additional users and endpoints---supports identifying and responding to movement across the environment using compromised or abused credentials.
The other tactics do not best fit this scenario:
Initial Access occurs earlier in the attack chain.
Credential Access focuses on obtaining credentials.
Privilege Escalation centers on increasing access rights.
Because the workflow is designed to detect and respond to movement between systems and identities, Option C (Lateral Movement) is the correct and verified answer.
What trigger will cause a Falcon Fusion Workflow to activate from Falcon Identity Protection?
Falcon Fusion workflows integrate directly with Falcon Identity Protection through identity-based triggers, allowing automated responses to identity threats. The correct trigger that activates a Falcon Fusion workflow from Identity Protection is Alert > Identity detection.
Identity detections are generated when Falcon observes suspicious or malicious identity behavior, such as credential abuse, abnormal authentication patterns, lateral movement attempts, or policy violations related to identity risk. These detections are distinct from endpoint-only detections or incidents and are specifically designed to represent identity-based attack activity.
While New incident and New endpoint detection are valid Falcon Fusion triggers in other Falcon modules, they are not the primary triggers for identity-focused automation. Similarly, Spotlight user action > Host relates to vulnerability management workflows rather than identity analytics.
The CCIS curriculum emphasizes that Falcon Fusion enables automated identity response, such as notifying security teams, disabling accounts, enforcing MFA, or triggering SOAR actions, based on identity detections. Therefore, workflows tied to Alert > Identity detection allow organizations to respond quickly and consistently to identity threats, making Option C the correct answer.
Which of the following is NOT a default insight but can be created with a custom insight?
In Falcon Identity Protection, default insights are prebuilt analytical views provided by CrowdStrike to immediately highlight common and high-impact identity risks across the environment. These default insights are automatically available in the Risk Analysis and Insights areas and are designed to surface well-known identity exposure patterns without requiring customization.
Examples of default insights include Using Unmanaged Endpoints, GPO Exposed Password, and Compromised Password. These insights are natively provided because they represent frequent and high-risk identity attack vectors such as credential exposure, unmanaged authentication sources, and password compromise, all of which directly contribute to elevated identity risk scores.
Poorly Protected Accounts with SPN (Service Principal Name), however, is not provided as a default insight. While Falcon Identity Protection does collect and analyze SPN-related risk signals---such as Kerberoasting exposure and weak service account protections---this specific grouping must be created by administrators using custom insight filters. Custom insights allow teams to define precise conditions, combine attributes (privilege level, SPN presence, password age, MFA status), and tailor risk visibility to their organization's threat model.
This distinction is emphasized in the CCIS curriculum, which explains that custom insights extend beyond default coverage, enabling deeper, organization-specific identity risk analysis. Therefore, Option D is the correct answer.
Unlock All Questions for CrowdStrike IDP Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 58 Questions & Answers