Most Recent F5 Networks F5CAB1 Exam Dumps
Prepare for the F5 Networks BIG-IP Administration Install, Initial Configuration, and Upgrade exam with our extensive collection of questions and answers. These practice Q&A are updated according to the latest syllabus, providing you with the tools needed to review and test your knowledge.
QA4Exam focus on the latest syllabus and exam objectives, our practice Q&A are designed to help you identify key topics and solidify your understanding. By focusing on the core curriculum, These Questions & Answers helps you cover all the essential topics, ensuring you're well-prepared for every section of the exam. Each question comes with a detailed explanation, offering valuable insights and helping you to learn from your mistakes. Whether you're looking to assess your progress or dive deeper into complex topics, our updated Q&A will provide the support you need to confidently approach the F5 Networks F5CAB1 exam and achieve success.
The questions for F5CAB1 were last updated on Apr 19, 2026.
- Viewing page 1 out of 8 pages.
- Viewing questions 1-5 out of 42 questions
modification]
An administrator is in the process of reactivating the license using the interface displayed in the exhibit.
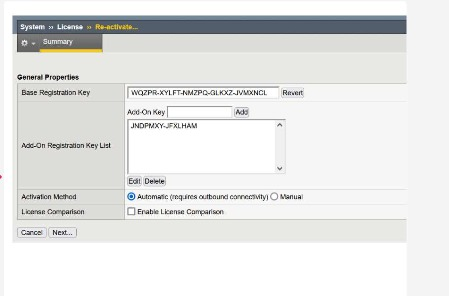
When you choose Automatic as the activation method in the License Re-activate screen, the BIG-IP device itself contacts F5's license activation service over the Internet.
For successful automatic activation:
The BIG-IP must have outbound network connectivity (typically via the management interface).
DNS resolution and routing must allow it to reach the F5 license activation host (the one shown in option D).
The device sends its dossier and registration key to that service and receives an updated license file in return, which is then installed automatically.
The other hostnames in the options are not used by BIG-IP for license activation, so they cannot be correct in the context of Automatic Activation.
The BIG-IP Administrator uses Secure Copy Protocol (SCP) to upload a TMOS image to the /shared/images/ directory in preparation for an upgrade.
After the upload is complete, what will the system do before the image appears in the GUI under:
System Software Management Image List?
When a TMOS ISO file is transferred to /shared/images/, the BIG-IP automatically performs a validation step:
Checksum Verification
Before the image becomes visible in the GUI, the system verifies the internal checksum embedded inside the ISO.
This ensures:
The file was fully transferred
The image is not corrupted
It matches the official F5 release signature
Only after passing this verification does the GUI display the ISO under ''Available Images.''
Why the other options are incorrect:
A . Reboot into a new partition
No reboot occurs simply from uploading an image.
C . Copying into /var/local/images/
This directory is not used for ISO storage.
All valid images remain in /shared/images/.
Thus, the correct system action is checksum verification.
How can the BIG-IP Administrator tell when an unlicensed module has been provisioned?
The BIG-IP system has built-in licensing enforcement.
If an administrator provisions a module that the device is not licensed to run, the system will still allow the provisioning action to occur initially, but the system detects the mismatch and displays an alert.
What actually happens:
The GUI places a warning banner in the upper-left corner labeled something similar to:
''Provisioning Warning''
This appears immediately after provisioning a module that is not included in the active license.
The system remains in an ''inconsistent state'' until the module is disabled again or the license is updated.
This is the visual cue BIG-IP uses to indicate that a module was provisioned without valid licensing.
Why the other options are incorrect:
A . ''A BIG-IP does not allow unlicensed modules to be provisioned.''
Not true. BIG-IP does allow provisioning, but warns afterward.
B . ''A warning will appear when provisioning an unlicensed module.''
The warning does not appear during the provisioning step itself.
It appears after provisioning, in the main GUI, as a system banner.
When logged into the bash shell of a BIG-IP system, which of the following commands will display the management-ip address?
(Choose two.)
When logged into the bash shell of a BIG-IP system, there are two valid ways to view the management-ip address:
A . tmsh list /sys management-ip
Even from the bash shell, the administrator can enter a tmsh command by typing:
tmsh list /sys management-ip
This displays:
Management IP address
Netmask
Any configured management routes
This is the official tmsh method for viewing the management-ip configuration.
C . ifconfig mgmt
In the underlying Linux OS, the management interface maps to the mgmt interface.
Running:
ifconfig mgmt
displays:
Assigned management IP
Netmask
Link-level status
This is a valid Linux-level method used frequently for troubleshooting.
Why the other options are incorrect:
B . show mgmt ip
Not a valid bash or tmsh command on BIG-IP.
D . list / sys management-ip
Missing the tmsh prefix.
In bash, this will generate a syntax error.
The correct form requires:
tmsh list /sys management-ip
A BIG-IP Administrator is responsible for deploying a new software image on an F5 BIG-IP HA pair and has scheduled a one-hour maintenance window.
With a focus on minimizing service disruption, which of the following strategies is the most appropriate?
For BIG-IP high-availability (HA) pairs, F5's recommended upgrade workflow prioritizes service continuity, predictable failover, and minimal downtime. The established best-practice sequence is:
Upgrade the standby unit first
Because the standby device is not passing traffic, upgrading and rebooting it does not impact production.
Boot the standby unit into the newly installed version
Once online, the administrator verifies basic health, device sync status, cluster communication, and module functionality.
Perform a controlled failover to the upgraded unit
Traffic shifts to the newly upgraded device, allowing validation of the configuration and operational behavior under real traffic loads.
Upgrade the second device (now standby)
The previously active device becomes standby after failover, allowing it to be safely upgraded and rebooted without interruption.
This phased approach ensures only one device is unavailable at a time, allowing continuous traffic flow throughout the upgrade process.
Why the Correct Answer is C
Option C exactly matches F5's documented production-safe upgrade method:
Upgrade the standby node first
Reboot into new image
Failover to upgraded device
Validate
Upgrade the remaining (now-standby) device
This procedure minimizes risk and traffic disruption.
Why the other options are incorrect:
A . Upgrade the active node first
Upgrading the active device requires removing it from service and failing over abruptly. This is not recommended and increases service disruption risk.
B . Resetting device trust
Resetting trust is unnecessary and can disrupt configuration sync, peer communication, and cluster operation. It is not part of any standard upgrade workflow.
D . Upgrading and rebooting both nodes simultaneously
This would cause total outage, because both HA members would be unavailable at the same time.
Unlock All Questions for F5 Networks F5CAB1 Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 42 Questions & Answers