Most Recent Fortinet FCP_FSM_AN-7.2 Exam Dumps
Prepare for the Fortinet FCP - FortiSIEM 7.2 Analyst exam with our extensive collection of questions and answers. These practice Q&A are updated according to the latest syllabus, providing you with the tools needed to review and test your knowledge.
QA4Exam focus on the latest syllabus and exam objectives, our practice Q&A are designed to help you identify key topics and solidify your understanding. By focusing on the core curriculum, These Questions & Answers helps you cover all the essential topics, ensuring you're well-prepared for every section of the exam. Each question comes with a detailed explanation, offering valuable insights and helping you to learn from your mistakes. Whether you're looking to assess your progress or dive deeper into complex topics, our updated Q&A will provide the support you need to confidently approach the Fortinet FCP_FSM_AN-7.2 exam and achieve success.
The questions for FCP_FSM_AN-7.2 were last updated on Apr 30, 2026.
- Viewing page 1 out of 6 pages.
- Viewing questions 1-5 out of 32 questions
Which two settings must you configure to allow FortiSIEM to apply tags to devices in FortiClient EMS? (Choose two.)
To allow FortiSIEM to apply tags to devices in FortiClient EMS, FortiEMS API credentials must be defined on FortiSIEM to enable communication with EMS, and FortiSIEM API credentials must be defined on FortiEMS to allow EMS to accept tagging instructions from FortiSIEM. This bidirectional API trust is essential for tag application.
Refer to the exhibit.
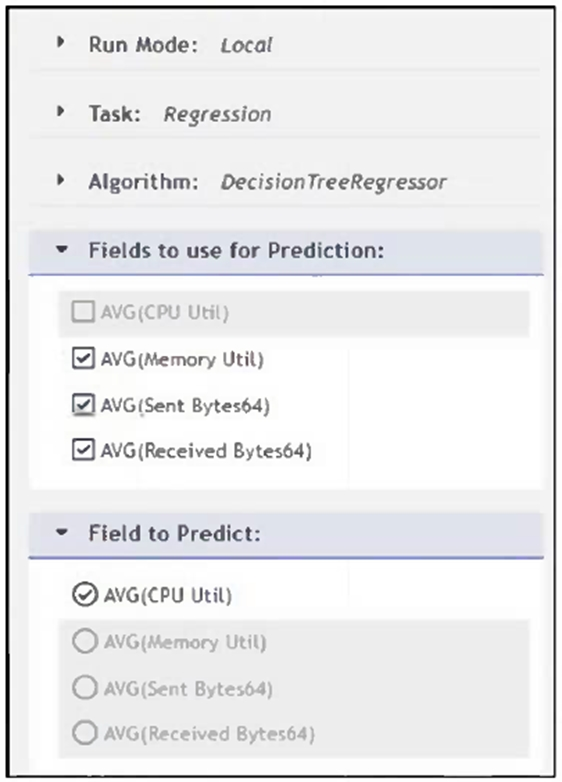
What will happen when a device being analyzed by the machine learning configuration shown in the exhibit has a consistently high memory utilization?
In the configuration shown, FortiSIEM uses Memory Util, Sent Bytes, and Received Bytes as input features to predict CPU Utilization via a regression model. If a device shows consistently high memory utilization, the model will incorporate that into its training data and update itself with a higher average value for memory utilization, influencing future CPU utilization predictions.
Refer to the exhibit.
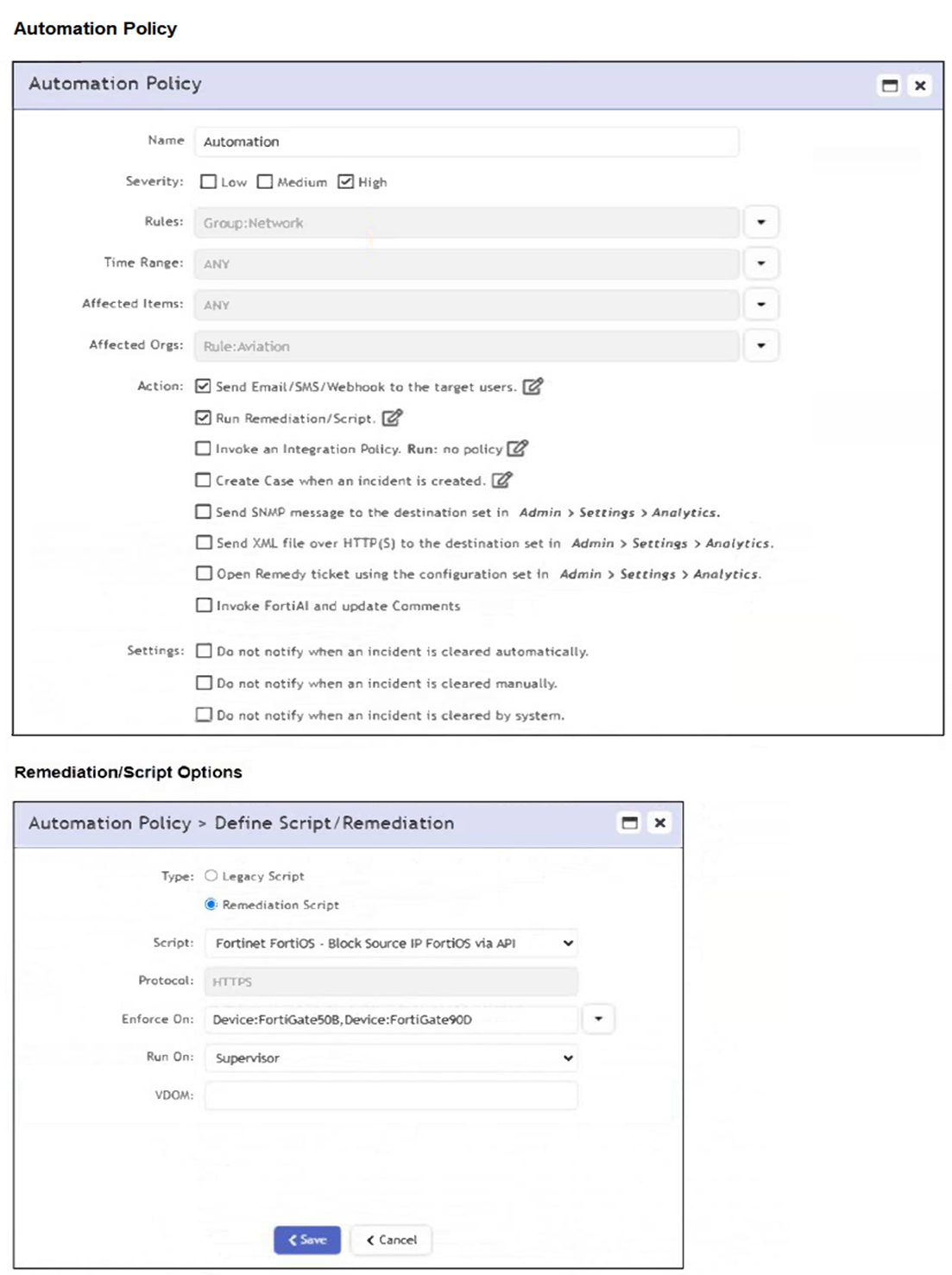
If a rule containing the automation policy shown in the exhibit triggers, what will happen?
The automation policy is configured to run a remediation script named 'Fortinet FortiOS - Block Source IP FortiOS via API'. It specifies enforcement on two FortiGate devices: FortiGate508 and FortiGate90D. Therefore, associated source IP addresses will be blocked on those two FortiGate firewalls only.
Refer to the exhibit.
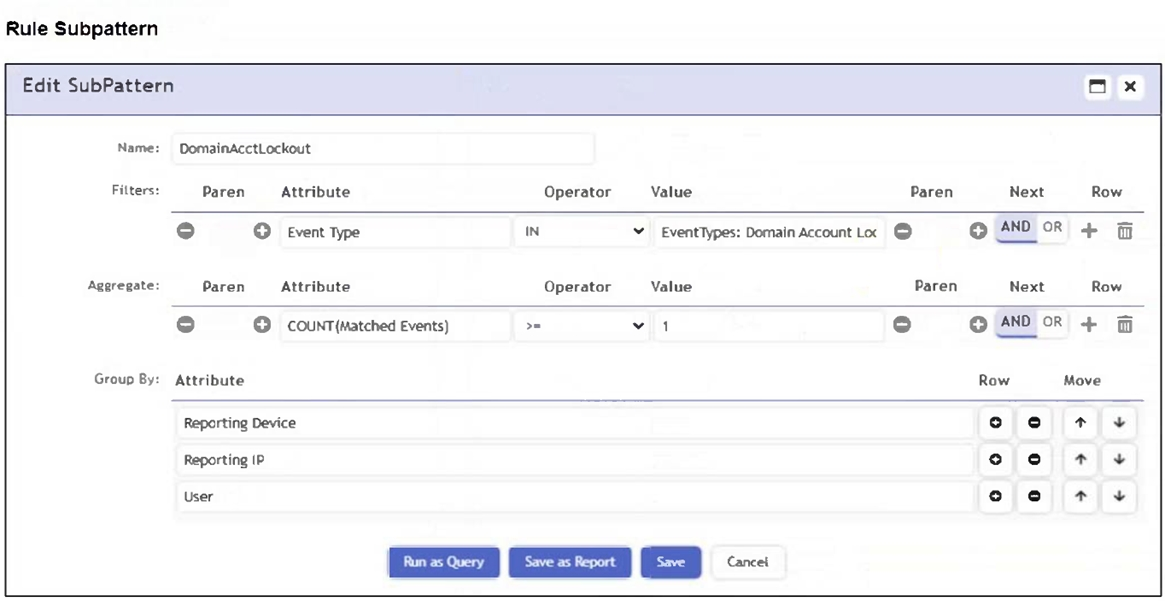
Which section contains the subpattern configuration that determines how many matching events are needed to trigger the rule?
The Aggregate section contains the condition COUNT(Matched Events) >= 1, which defines how many events must match the filter criteria for the rule to trigger. This is the subpattern configuration that determines the event threshold.
Refer to the exhibit.
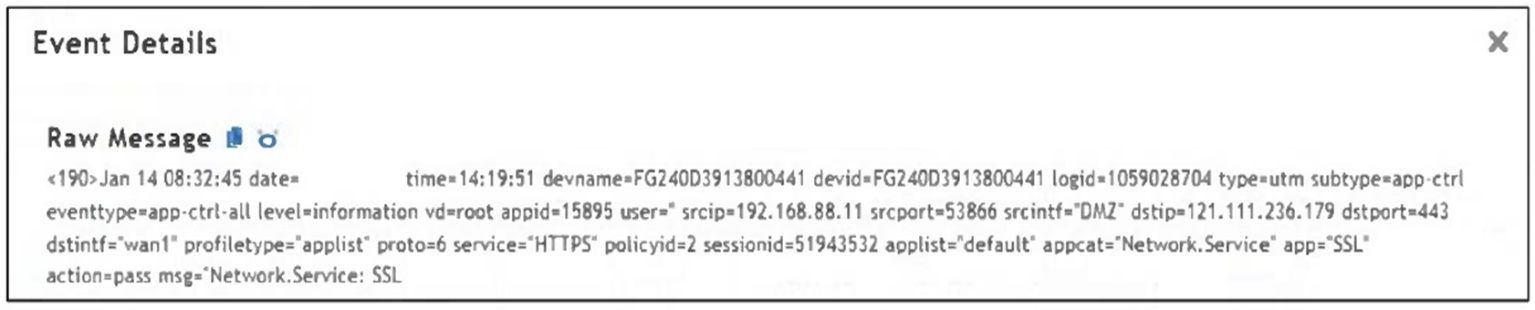
Which value would you expect the FortiSIEM parser to use to populate the Application Name field?
The Application Name field in FortiSIEM is typically populated using the value of the app field in the raw log. In this event, app='SSL', so 'SSL' is the expected application name parsed by FortiSIEM.
Unlock All Questions for Fortinet FCP_FSM_AN-7.2 Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 32 Questions & Answers