Most Recent Fortinet FCSS_LED_AR-7.6 Exam Dumps
Prepare for the Fortinet NSE 6 - LAN Edge 7.6 Architect exam with our extensive collection of questions and answers. These practice Q&A are updated according to the latest syllabus, providing you with the tools needed to review and test your knowledge.
QA4Exam focus on the latest syllabus and exam objectives, our practice Q&A are designed to help you identify key topics and solidify your understanding. By focusing on the core curriculum, These Questions & Answers helps you cover all the essential topics, ensuring you're well-prepared for every section of the exam. Each question comes with a detailed explanation, offering valuable insights and helping you to learn from your mistakes. Whether you're looking to assess your progress or dive deeper into complex topics, our updated Q&A will provide the support you need to confidently approach the Fortinet FCSS_LED_AR-7.6 exam and achieve success.
The questions for FCSS_LED_AR-7.6 were last updated on Apr 27, 2026.
- Viewing page 1 out of 8 pages.
- Viewing questions 1-5 out of 40 questions
Refer to the exhibits.
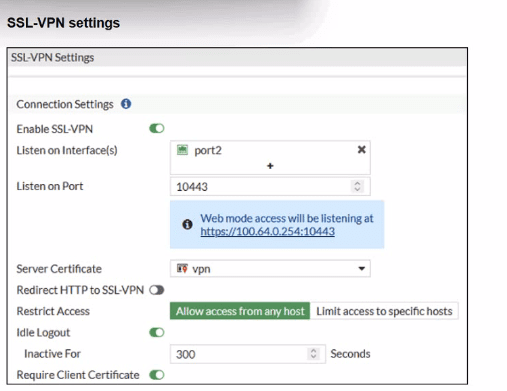
Which include debug output and SSL VPN configuration details.
An SSL VPN has been configured on FortiGate. To enhance security, the administrator enabled Required Client Certificate in the SSL VPN settings. However, when a user attempts to connect, authentication fails.
Which configuration change is needed to fix the issue and allow the user to connect?
The SSL-VPN configuration hasRequire Client Certificateenabled. When this is enabled, FortiOS performs two checks:
Normal user authentication(username/password or PKI user)
Additional client certificate check-- the client certificatemust be signed by a CA that FortiGate trusts
FortiOS documentation for ''SSL VPN with certificate authentication'' states:
''The client certificate only needs to be signed by a known CA in order to pass authentication.''
''The CA certificate is the certificate that signed both the server certificate and the user certificate... The CA certificate is available to be imported on the FortiGate.''
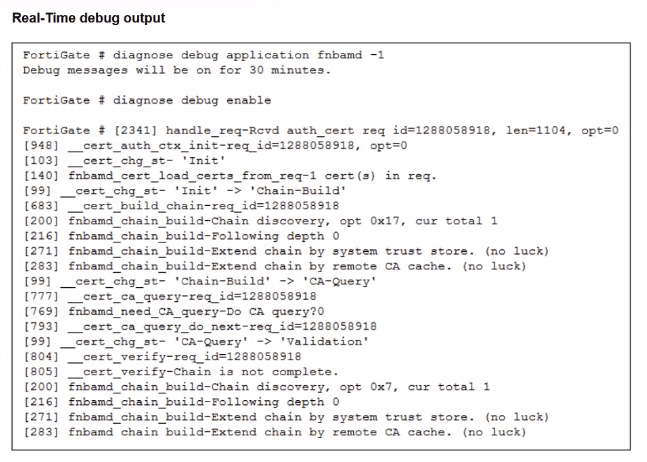
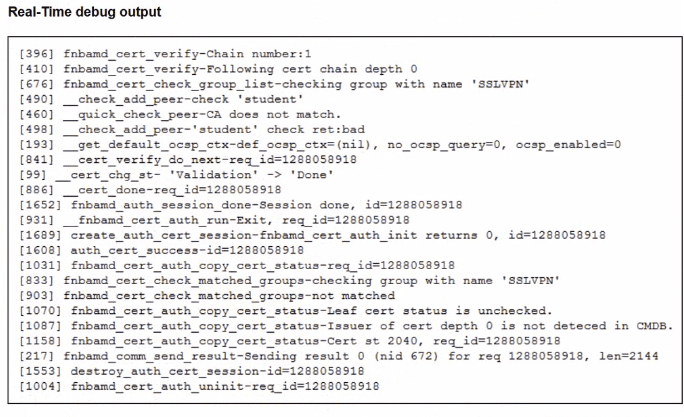
The debug output shows key lines:
__quick_check_peer-CA does not match.
Issuer of cert depth 0 is not detected in CMDB.
This tells us:
FortiGatedoes see the user's certificate,
Butcannot find the issuing CAin its local CA certificate store (''CMDB'' = configuration database).
This means theCA that signed the user certificate has not been importedinto FortiGate.
Now evaluate the options:
A . Enable Redirect HTTP to SSL-VPN-- affects only redirection from HTTP to HTTPS; it has nothing to do with certificate validation.
B . Import the CA that signed the SSL VPN Server Certificate-- the server certificate is already working (the portal comes up) and its CA is not what the debug complains about; the error is about thepeer (user) certificate. Often the same CA signs both, but the failing check specifically says the issuer of the client cert is not in CMDB.
C . Set the user certificate as the Server Certificate-- incorrect; server and client certificates serve different roles.
D . Import the CA that signed the user certificate to FortiGate-- this directly addresses the debug error and aligns with the documented requirement that the CA which issued the user certificate must be known to FortiGate.
A network engineer is deploying FortiGate devices using zero-touch provisioning (ZTP). The devices must automatically connect to FortiManager and receive their configurations upon first boot. However, after powering on the devices, they fail to register with FortiManager.
What could be a possible cause of this issue?
Zero-Touch Provisioning (ZTP) for FortiGate devices is handled throughFortiDeploy, which automatically connects a FortiGate toFortiManagerso the device can download configuration templates and be centrally managed.
For ZTP to work, the newly booted FortiGate must successfully reach FortiManager. One of thecritical requirementsis connectivity over theFGFM (FortiGate--FortiManager) management protocol, which uses:
TCP Port 541
This is clearly stated in multiple Fortinet documents:
FortiGate Cloud Admin Guidelists port541as the management channel used for FortiGate FortiManager / FortiGate Cloud communications:''Management... Protocol: TCP, Port:541''
FortiOS Administration Guidealso confirms this:''FortiManager provides remote management of FortiGate devices overTCP port 541.''
Since ZTP uses FortiDeploy to push the FortiManager IP to the device and relies on FGFM (port 541) for registration and configuration delivery,any failure on this port breaks the entire ZTP workflow.
Why option D is correct
If the FortiGate cannot reach FortiManager onTCP/541, itcannot register, cannot be authorized, and cannot receive its configuration --- leading to a ZTP failure.
This is themost common causein real deployments:
Firewall blocking TCP/541
Upstream NAT device not forwarding 541
ISP restrictions
Incorrect FortiManager IP or routing issue
ZTP device behind a network that does not allow outbound 541
Why the other options are incorrect
A . The FortiGate device requires manual intervention to accept the FortiManager connection.
Incorrect.
ZTP is built specifically to avoid manual intervention. Once the FortiDeploy key is used, the device auto-connects to FortiManager without needing local acceptance.
B . ZTP works only when devices are connected using a console cable.
Incorrect.
ZTP requiresno console cable--- that's the whole point. It relies on DHCP, WAN connectivity, and FortiDeploy auto-join.
C . The FortiGate device must be preloaded with a configuration file before ZTP can function.
Incorrect.
Preloading configuration defeats the purpose of ZTP.
ZTP delivers the initial configuration automatically from FortiManager using FortiDeploy.
LAN Edge 7.6 Architect Context
LAN Edge deployments often use FortiManager as the central orchestrator for:
FortiSwitch management via FortiLink
FortiAP wireless provisioning
SD-Branch configuration templates
Security Fabric automation
For all of this, ZTP enables remote sites to deploy FortiGate, FortiSwitch, and FortiAP withno on-site expertise.
If TCP/541 to FortiManager is blocked, the entire LAN Edge deployment pipeline fails, making optionDthe only valid and document-supported answer.
Refer to the exhibits.
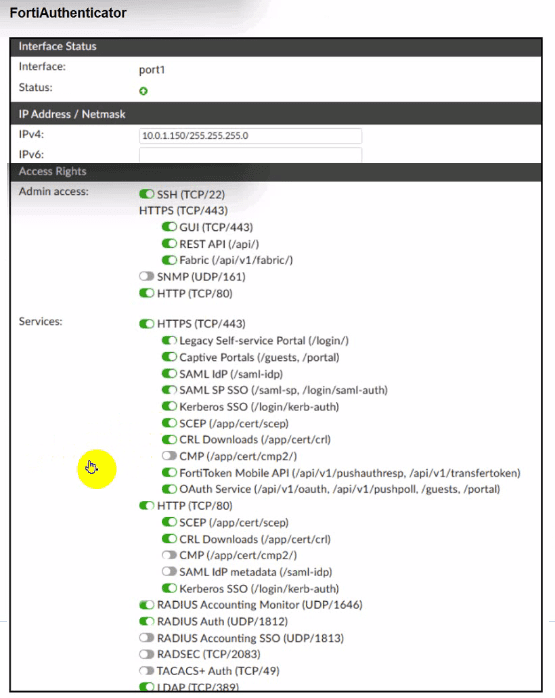
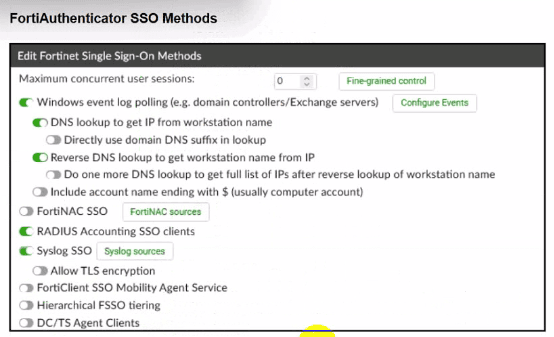
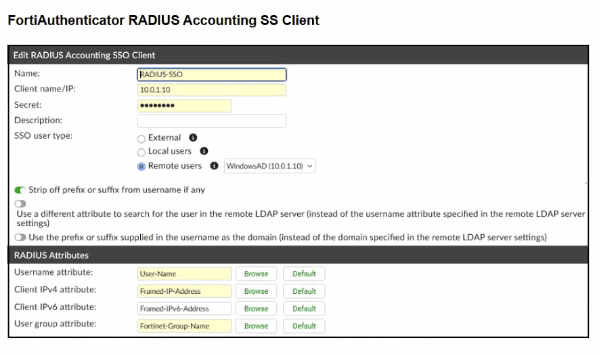
A company has multiple FortiGate devices deployed and wants to centralize user authentication and authorization. The administrator decides to use FortiAuthenticator to convert RSSO messages to FSSO, allowing all FortiGate devices to receive user authentication updates.
After configuring FortiAuthenticator to receive RADIUS accounting messages, users can authenticate, but FortiGate does not enforce the correct policies based on user groups. Upon investigation, the administrator discovers that FortiAuthenticator is receiving RADIUS accounting messages from the RADIUS server and successfully queries LDAP for user group information. But, FSSO updates are not being sent to FortiGate devices and FortiGate firewall policies based on FSSO user groups are not being applied.
What is the most likely reason FortiGate is not receiving FSSO updates?
In this design, FortiAuthenticator receivesRADIUS accounting (RSSO) messages, looks up the user in LDAP to get group information, theninjects FSSO logon eventstoward all FortiGate devices.
From the exhibits we know:
FortiAuthenticatoris receiving RADIUS accountingfrom the RADIUS server.
LDAP queries are successful and return group membership.
But FortiGatedoes not receive FSSO logons, so identity-based policies are not applied.
For FortiAuthenticator to create an FSSO logon, the RADIUS accounting record must be correctlyparsed into at least:
Username
Client IP address
These are mapped from the RADIUS attributes in theRADIUS Accounting SSO clientconfiguration (for example, User-Name and Framed-IP-Address). If these are not defined or mapped incorrectly, FortiAuthenticator can see the accounting packet butcannot build a valid FSSO session, so no update is sent to FortiGate.
Thus the most likely root cause is:
The RADIUS Username and Client IPv4 attributes are not correctly definedfor that RADIUS Accounting SSO client (optionA).
Other options conflict with the scenario:
B-- LDAP is already successfully returning groups.
C-- FSSO user group attribute is separate; even without it, FSSO logons would still be created (just without group mapping).
D-- The interfaceisreceiving RADIUS accounting, so it is clearly enabled.
Why is it critical to maintain NTP synchronization between FortiGate and FortiSwitch when FortiLink is configured?
FortiGate and FortiSwitchmust share synchronized timewhen operating in FortiLink mode.
Documented reasons in FortiOS:
Accurate time synchronization is required for logs, authentication events, and fabric correlations.
Why it's critical:
802.1X EAP and RADIUS timestamp validation
NAC policy enforcement timestamps
Certificate validation
Log correlation in Security Fabric / FortiAnalyzer
Incorrect options:
A: Firmware synchronization does NOT require NTP.
B: Switch-to-switch communication does not depend on NTP.
D: Standalone mode is unrelated to time sync.
Refer to the exhibits.
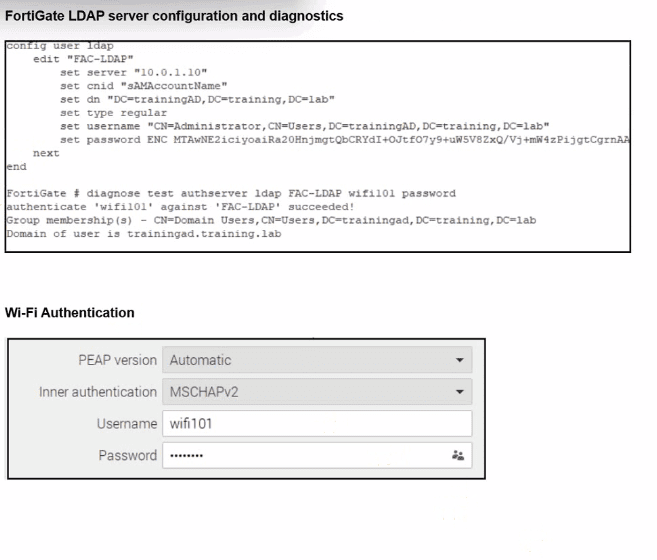
An LDAP server has been successfully configured on FortiGate. which forwards LDAP authentication requests to a Windows Active Directory (AD) server. Wireless users report that they are unable to authenticate. Upon troubleshooting, you find that authentication fails when using MSCHAPv2.
What is the most likely reason for this issue?
From the exhibit, LDAP on FortiGate is correctly configured and tested:
diagnose test authserver ldap FAC-LDAP wifi101 password
authenticate 'wifi101' against 'FAC-LDAP' succeeded!
Group membership(s) - CN=Domain Users,...
So:
LDAP connectivity works
Bind DN, DN, CNID, and credentials are correct(so optionCis eliminated).
Firewall policies do not affect the802.1X / Wi-Fi authentication stepitself, soAis not the root cause.
Nothing in the scenario indicates that AD is enforcing LDAPS-only; the LDAP test already succeeds using the configured parameters, soBis also excluded.
The Wi-Fi supplicant is configured forPEAP with inner authentication = MSCHAPv2.
MSCHAPv2 is achallenge--response mechanism designed for RADIUS, not for LDAP simple bind. FortiGate's LDAP implementation uses asimple bind (username/password) over LDAP or LDAPS, and it doesnotimplement MSCHAPv2 against LDAP backends.
In Fortinet's design, if you needPEAP-MSCHAPv2 with Active Directory, you must use:
ARADIUS server(such as Windows NPS or FortiAuthenticator), and
Have FortiGate use RADIUS,notLDAP, as the authentication backend for 802.1X / Wi-Fi users.
Because FortiGate cannot process MSCHAPv2 exchanges directly against an LDAP server, authentication fails when the inner method is MSCHAPv2, even though LDAP works when tested with a simple bind from the CLI.
Unlock All Questions for Fortinet FCSS_LED_AR-7.6 Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 40 Questions & Answers