Most Recent Fortinet FCSS_SASE_AD-24 Exam Dumps
Prepare for the Fortinet FCSS - FortiSASE 24 Administrator exam with our extensive collection of questions and answers. These practice Q&A are updated according to the latest syllabus, providing you with the tools needed to review and test your knowledge.
QA4Exam focus on the latest syllabus and exam objectives, our practice Q&A are designed to help you identify key topics and solidify your understanding. By focusing on the core curriculum, These Questions & Answers helps you cover all the essential topics, ensuring you're well-prepared for every section of the exam. Each question comes with a detailed explanation, offering valuable insights and helping you to learn from your mistakes. Whether you're looking to assess your progress or dive deeper into complex topics, our updated Q&A will provide the support you need to confidently approach the Fortinet FCSS_SASE_AD-24 exam and achieve success.
The questions for FCSS_SASE_AD-24 were last updated on Jun 5, 2026.
- Viewing page 1 out of 11 pages.
- Viewing questions 1-5 out of 54 questions
Refer to the exhibit.
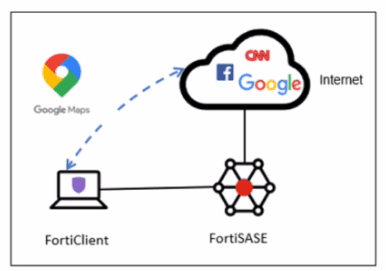
A company has a requirement to inspect all the endpoint internet traffic on FortiSASE, and exclude Google Maps traffic from the FortiSASE VPN tunnel and redirect it to the endpoint physical Interface.
Which configuration must you apply to achieve this requirement?
To meet the requirement of inspecting all endpoint internet traffic on FortiSASE while excluding Google Maps traffic from the FortiSASE VPN tunnel and redirecting it to the endpoint's physical interface, you should configure split tunneling. Split tunneling allows specific traffic to bypass the VPN tunnel and be routed directly through the endpoint's local interface.
Split Tunneling Configuration:
Split tunneling enables selective traffic to be routed outside the VPN tunnel.
By configuring the Google Maps Fully Qualified Domain Name (FQDN) as a split tunneling destination, you ensure that traffic to Google Maps bypasses the VPN tunnel and uses the endpoint's local interface instead.
Implementation Steps:
Access the FortiSASE endpoint profile configuration.
Add the Google Maps FQDN to the split tunneling destinations list.
This configuration directs traffic intended for Google Maps to bypass the VPN tunnel and be routed directly through the endpoint's physical network interface.
FortiOS 7.2 Administration Guide: Provides details on split tunneling configuration.
FortiSASE 23.2 Documentation: Explains how to set up and manage split tunneling for specific destinations.
Which policy type is used to control traffic between the FortiClient endpoint to FortiSASE for secure internet access?
A FortiSASE administrator is configuring a Secure Private Access (SPA) solution to share endpoint information with a corporate FortiGate.
Which three configuration actions will achieve this solution? (Choose three.)
FortiOS 7.2 Administration Guide: Provides details on configuring Secure Private Access and integrating with FortiGate.
FortiSASE 23.2 Documentation: Explains how to set up and manage connections between FortiSASE and corporate FortiGate.
How does FortiSASE hide user information when viewing and analyzing logs?
FortiSASE hides user information when viewing and analyzing logs by hashing data using salt. This approach ensures that sensitive user information is obfuscated, enhancing privacy and security.
Hashing Data with Salt:
Hashing data involves converting it into a fixed-size string of characters, which is typically a hash value.
Salting adds random data to the input of the hash function, ensuring that even identical inputs produce different hash values.
This method provides enhanced security by making it more difficult to reverse-engineer the original data from the hash value.
Security and Privacy:
Using salted hashes ensures that user information remains secure and private when stored or analyzed in logs.
This technique is widely used in security systems to protect sensitive data from unauthorized access.
FortiOS 7.2 Administration Guide: Provides information on log management and data protection techniques.
FortiSASE 23.2 Documentation: Details on how FortiSASE implements data hashing and salting to secure user information in logs.
Which two deployment methods are used to connect a FortiExtender as a FortiSASE LAN extension? (Choose two.)
There are two deployment methods used to connect a FortiExtender as a FortiSASE LAN extension:
Connect FortiExtender to FortiSASE using FortiZTP:
FortiZero Touch Provisioning (FortiZTP) simplifies the deployment process by allowing FortiExtender to automatically connect and configure itself with FortiSASE.
This method requires minimal manual configuration, making it efficient for large-scale deployments.
Enter the FortiSASE domain name in the FortiExtender GUI as a static discovery server:
Manually configuring the FortiSASE domain name in the FortiExtender GUI allows the extender to discover and connect to the FortiSASE infrastructure.
This static discovery method ensures that FortiExtender can establish a connection with FortiSASE using the provided domain name.
FortiOS 7.2 Administration Guide: Details on FortiExtender deployment methods and configurations.
FortiSASE 23.2 Documentation: Explains how to connect and configure FortiExtender with FortiSASE using FortiZTP and static discovery.
Unlock All Questions for Fortinet FCSS_SASE_AD-24 Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 54 Questions & Answers