Most Recent Fortinet NSE5_SSE_AD-7.6 Exam Dumps
Prepare for the Fortinet NSE 5 - FortiSASE and SD-WAN 7.6 Core Administrator exam with our extensive collection of questions and answers. These practice Q&A are updated according to the latest syllabus, providing you with the tools needed to review and test your knowledge.
QA4Exam focus on the latest syllabus and exam objectives, our practice Q&A are designed to help you identify key topics and solidify your understanding. By focusing on the core curriculum, These Questions & Answers helps you cover all the essential topics, ensuring you're well-prepared for every section of the exam. Each question comes with a detailed explanation, offering valuable insights and helping you to learn from your mistakes. Whether you're looking to assess your progress or dive deeper into complex topics, our updated Q&A will provide the support you need to confidently approach the Fortinet NSE5_SSE_AD-7.6 exam and achieve success.
The questions for NSE5_SSE_AD-7.6 were last updated on Apr 29, 2026.
- Viewing page 1 out of 7 pages.
- Viewing questions 1-5 out of 36 questions
You have a FortiGate configuration with three user-defined SD-WAN zones and one or two members in each of these zones. One SD-WAN member is no longer used in health-check and SD-WAN rules. This member is the only member of its zone. You want to delete it.
What happens if you delete the SD-WAN member from the FortiGate GUI?
Questions no: 9 Verified Answer: B
Comprehensive and Detailed Explanation with all FortiSASE and SD-WAN 7.6 Core Administrator curriculum documents: According to the SD-WAN 7.6 Core Administrator study guide and FortiOS 7.6 Administration Guide, the behavior for deleting an SD-WAN member from the GUI when it is the only member in its zone is governed by the following operational logic:
Reference Checks: Before allowing the deletion of any SD-WAN member, FortiOS performs a 'check for dependencies.' If an interface is being used in an active Performance SLA or an SD-WAN Rule, the GUI will typically prevent the deletion or gray out the option until those references are removed. However, the question specifies that this member is no longer used in health-checks or rules.
Zone Integrity: Unlike some other network objects, an SD-WAN zone is permitted to exist without any members. When you delete the final member of a user-defined zone through the GUI, the zone itself remains in the configuration as an empty container.
Route Management: When an SD-WAN member is deleted, any static routes that were specifically tied to that interface's membership in the SD-WAN bundle are automatically updated or removed by the FortiGate to prevent routing loops or 'black-holing' traffic. This is part of the automated cleanup process handled by the FortiOS management plane.
GUI vs. CLI: In the GUI, the process is streamlined to allow the removal of the member interface. Once the member is deleted, the interface returns to being a 'regular' system interface and can be used for standard firewall policies or other functions.
Why other options are incorrect:
Option A: There is no requirement that a zone must contain at least one member; 'empty' zones are valid configuration objects in FortiOS 7.6.
Option C: While the deletion is accepted, it is not with 'no further action'---the system must still reconcile the routing table and interface status.
Option D: FortiGate does not automatically move deleted members into the default zone (virtual-wan-link). Once deleted, the interface is simply no longer an SD-WAN member.
Which three authentication sources support secure identity verification and access control for FortiSASE remote users? (Choose three.)
An SD-WAN member is no longer used to steer SD-WAN traffic. You want to update the SD-WAN configuration and delete the unused member.
Which action should you take first? (Choose one answer)
According to the SD-WAN 7.6 Core Administrator study guide and the Fortinet Document Library, FortiOS maintains strict referential integrity for SD-WAN objects. An SD-WAN member interface cannot be deleted or removed from the configuration if it is still being 'used' or referenced by other features.
Reference Locking: In the FortiOS GUI, the 'Delete' button for an SD-WAN member is typically grayed out or an error message appears if the interface is part of an active service or monitoring tool.
Performance SLA Dependency: Performance SLAs (health checks) monitor specific member interfaces. If an interface is a participant in an SLA, it is considered 'active' by the system. Therefore, a critical first step in the decommissioning process is to remove the member from all Performance SLA definitions. Once the health check is no longer polling that interface, one major reference lock is released.
Other Dependencies: While firewall policies and SD-WAN rules (service rules) also create references, the question specifies the member is 'no longer used to steer traffic,' implying it may have already been removed from steering rules. However, Performance SLAs often remain active in the background, making their removal the essential next step to permit the deletion of the member itself.
Why other options are incorrect:
Option A: Moving a member between zones doesn't help you delete it; it just changes its logical grouping. It still remains an active SD-WAN member.
Option B: Disabling the physical interface does not remove the configuration references within the SD-WAN engine. The FortiGate will simply report the member as 'Down,' but it will still exist in the configuration as a member.
Option D: In modern SD-WAN deployments, static routes usually point to the SD-WAN Zone (like virtual-wan-link) rather than individual physical interfaces. Therefore, you don't typically need to delete the static route to remove a single member from the zone.
Which FortiSASE feature monitors SaaS application performance and connectivity to points of presence (POPs)?
According to the FortiSASE 7.6 Administration Guide and Digital Experience Monitoring (DEM) documentation, the feature specifically designed to monitor SaaS application performance and connectivity to PoPs is Digital Experience Monitoring (DEM).
SaaS and Path Visibility: DEM assists administrators in troubleshooting remote user connectivity issues by providing enhanced health check visibility for SaaS applications, endpoint devices, and the network path. It provides real-time insights into application performance and latency issues.
PoP Connectivity: It monitors the digital journey from the end-user device through the Security Points of Presence (POPs) to the final application, identifying hops where degraded service (packet loss, delay, or jitter) is detected.
Proactive Management: By establishing thresholds and simulating user activities through Synthetic Transaction Monitoring (STM), DEM allows IT teams to identify performance problems before they impact the business.
Why other options are incorrect:
Option A: Operations widgets provide general status overviews but do not offer the granular per-hop path analysis or specific SaaS transaction monitoring found in DEM.
Option B: FortiView dashboards provide traffic visibility and session data but are not dedicated performance monitoring tools for end-to-end digital experience.
Option C: Event logs record system occurrences and security events but do not provide real-time performance metrics or health check probes for SaaS applications.
Refer to the exhibit.
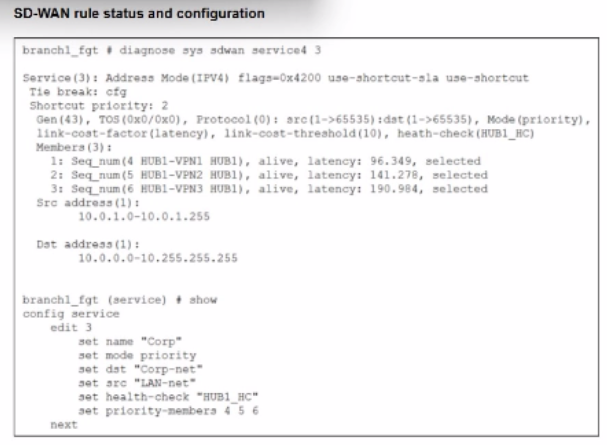
The SD-WAN rule status and configuration is shown. Based on the exhibit, which change in the measured latency will first make HUB1-VPN3 the new preferred member?
According to the SD-WAN 7.6 Core Administrator study guide and the FortiOS 7.6 Administration Guide, the selection of a preferred member in a Best Quality (priority) rule is determined by the measured quality metric (latency, in this case) and the link-cost-threshold.
Rule Logic (Best Quality): In the exhibit, the SD-WAN rule is configured with set mode priority, which corresponds to the Best Quality strategy. This strategy ranks members based on the link-cost-factor, which is set to latency.
The Link-Cost-Threshold: The exhibit shows link-cost-threshold(10), which is the default 10% value. This threshold is designed to prevent 'link flapping'. To replace the current preferred member, a new member must not only have a better latency but must be better by more than 10%.
The Calculation:
The current preferred member is HUB1-VPN1 with a real latency of 96.349 ms.
To calculate the 'target' latency a lower-priority member must achieve to take over, we use the formula: $Target = \frac{Current\_Latency}{(1 + \frac{Threshold}{100})}$.
$\frac{96.349}{1.1} = \mathbf{87.59\text{ ms}}$.
Evaluating Options:
Option A (80 ms): Since 80 ms is lower than the required 87.59 ms target, HUB1-VPN3 successfully overcomes the 10% advantage of HUB1-VPN1 and becomes the new preferred member.
Option D (90 ms): While 90 ms is lower than 96.349 ms, it is not lower than 87.59 ms. Therefore, the 10% threshold prevents a member switch, and HUB1-VPN1 remains preferred.
Option B: Incorrect because having a 'lower' latency is not enough due to the 10% threshold.
Option C: If HUB1-VPN1 moved to 200 ms, HUB1-VPN2 (at 141.278 ms) would likely become the new preferred member before HUB1-VPN3 (at 190.984 ms).
Unlock All Questions for Fortinet NSE5_SSE_AD-7.6 Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 36 Questions & Answers