Fortinet NSE7_SSE_AD-25 Dumps - Pass Fortinet NSE 7 - FortiSASE 25 Enterprise Administrator Exam in First Attempt 2026
The Fortinet NSE7_SSE_AD-25 exam, also known as the Fortinet NSE 7 - FortiSASE 25 Enterprise Administrator exam, is part of the Fortinet Certified Solution Specialist, FCSS Fortinet Certified Solution Specialist Secure Access Service Edge certification track. It is designed for professionals who manage and secure SASE environments and want to validate their practical understanding of FortiSASE. This exam matters because it demonstrates the ability to deploy, integrate, and manage secure access services in modern enterprise networks. Earning this certification can help show that you are prepared for real-world SASE administration tasks.
Exam Topics and Approximate Weightage
| # | Exam Topics | Sub-Topics | Approximate Weightage (%) |
|---|---|---|---|
| 1 | SASE architecture and integration | FortiSASE components, integration with enterprise networks, identity and access design, traffic flow and policy alignment | 30% |
| 2 | SASE deployment and management | Deployment planning, configuration tasks, policy administration, service monitoring and operational management | 30% |
| 3 | Secure Private Access (SPA) | Access control setup, private application access, user and group policy, secure connectivity validation | 20% |
| 4 | Analytics | Log review, reporting insights, event analysis, security and usage visibility | 20% |
This exam tests more than memorization. Candidates need a solid grasp of FortiSASE concepts, deployment workflows, and management tasks, along with the ability to interpret analytics and apply secure access principles in practical scenarios. It is designed to measure both knowledge depth and day-to-day administrative readiness.
How QA4Exam.com Helps You Pass
QA4Exam.com offers the Exam PDF with actual questions and answers, plus an Online Practice Test that helps you prepare with confidence for the Fortinet NSE7_SSE_AD-25 exam. The practice test gives you a real exam simulation so you can get familiar with the question style and improve your time management. The questions are updated and verified, helping you focus on the most relevant exam content. With both the PDF and practice test, you can strengthen your preparation and work toward passing on your first attempt.
Frequently Asked Questions
1. Who should take the Fortinet NSE7_SSE_AD-25 exam?
This exam is for professionals working with FortiSASE and secure access service edge environments who want to validate their enterprise administration skills as part of the FCSS Secure Access Service Edge certification track.
2. Is the Fortinet NSE 7 - FortiSASE 25 Enterprise Administrator exam difficult?
It can be challenging because it tests practical knowledge of SASE architecture, deployment, SPA, and analytics. Candidates who understand real FortiSASE administration tasks are usually better prepared.
3. Can I pass with only braindumps?
Braindumps alone are not a complete preparation method. They are most effective when combined with hands-on understanding and practice so you can handle different question styles and scenarios.
4. Do I need hands-on experience for NSE7_SSE_AD-25?
Hands-on experience is very helpful because the exam focuses on deployment, management, integration, and operational knowledge. Practical familiarity makes it easier to understand the correct answers.
5. Are QA4Exam.com dumps and practice tests enough to prepare?
They are a strong preparation resource because they provide verified answers, updated questions, and a realistic practice format. Many candidates use them to reinforce study and improve exam readiness.
6. How do the QA4Exam.com practice tests help with first-attempt success?
The online practice test simulates the exam environment, helps you manage time, and shows you how questions may appear in the real test. This can improve confidence and reduce surprises on exam day.
7. What format do the QA4Exam.com study materials use?
QA4Exam.com provides an Exam PDF with actual questions and answers and an Online Practice Test for interactive preparation. Both formats are designed to support efficient study and exam simulation.
The questions for NSE7_SSE_AD-25 were last updated on Jun 3, 2026.
- Viewing page 1 out of 16 pages.
- Viewing questions 1-5 out of 81 questions
Which statement about FortiSASE and SAML is true? (Choose one answer)
FortiSASE utilizes Security Assertion Markup Language (SAML) to provide a seamless Single Sign-On (SSO) experience for remote users connecting to the cloud infrastructure.
Role Identification: In a SAML exchange, FortiSASE functions as the Service Provider (SP). It relies on an external Identity Provider (IdP)---such as Microsoft Entra ID (formerly Azure AD), Okta, or FortiAuthenticator---to authenticate the user's identity and provide security assertions.2
SAML Group Matching: One of the core features of the FortiSASE SAML implementation is the ability to perform group matching. During the authentication process, the IdP sends a SAML assertion that typically includes an 'Attribute Statement' containing the user's group memberships.3 FortiSASE captures this attribute and matches it against locally defined SAML user groups.
Policy Enforcement: This group matching capability is critical because it allows administrators to apply different Security Internet Access (SIA) or Secure Private Access (SPA) policies based on the user's role (e.g., 'Marketing' vs. 'Finance') rather than managing individual users manually.
Analysis of Incorrect Options: * Options C and D are incorrect because FortiSASE does not natively act as a SAML IdP; it is designed to consume assertions from professional identity management platforms.
Option B is incorrect because FortiSASE fully supports and relies upon group matching for enterprise-scale policy management.
Refer to the exhibits.
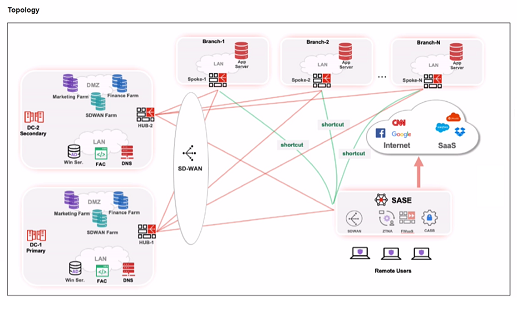

When remote users connected to FortiSASE require access to internal resources on Branch-2. how will traffic be routed?
When remote users connected to FortiSASE require access to internal resources on Branch-2, the following process occurs:
SD-WAN Capability:
FortiSASE leverages SD-WAN to optimize traffic routing based on performance metrics and priorities.
In the priority settings, HUB-1 is configured with the highest priority (P1), whereas HUB-2 has a lower priority (P2).
Traffic Routing Decision:
FortiSASE evaluates the available hubs (HUB-1 and HUB-2) and selects HUB-1 due to its highest priority setting.
Once the traffic reaches HUB-1, it is then routed to the appropriate branch based on internal routing policies.
Branch-2 Access:
Since HUB-1 has the highest priority, FortiSASE directs the traffic to HUB-1.
HUB-1 then routes the traffic to Branch-2, providing the remote users access to the internal resources.
FortiOS 7.6 Administration Guide: Details on SD-WAN configurations and priority settings.
FortiSASE 23.2 Documentation: Explains how FortiSASE integrates with SD-WAN to route traffic based on defined priorities and performance metrics.
Which information does FortiSASE use to bring network lockdown into effect on an endpoint? (Choose one answer)
The Network Lockdown feature in FortiSASE is a specialized security control designed to ensure that managed endpoints remain protected by the SASE security stack at all times.
Mechanism of Action: Network lockdown relies specifically on the connection status of the tunnel to FortiSASE. When this feature is enabled in the Endpoint Profile, the FortiClient agent monitors whether the secure VPN tunnel (SSL or IPsec) to a FortiSASE Point of Presence (PoP) is active.
Enforcement Logic: If the agent detects that the tunnel is disconnected, it immediately places the endpoint's network interface into a 'locked' state. In this state, all inbound and outbound network traffic is blocked, with the exception of traffic required to re-establish the connection to the FortiSASE infrastructure.
Purpose: This prevents 'leakage' where an endpoint might communicate directly with the internet without inspection if the VPN tunnel drops or is manually disabled by the user. It essentially mandates that the device is either connected to FortiSASE or has no network access at all.
Analysis of Incorrect Options:
Option A and B: While malware and vulnerabilities affect the security posture, they trigger different remediation actions (like quarantine or patching) rather than the 'Network Lockdown' tunnel-state feature.
Option D: ZTNA tags identify the security posture to allow or deny access to specific applications, whereas Network Lockdown is a binary state (On/Off) affecting all network traffic based purely on tunnel connectivity.
You have configured FortiSASE Secure Private Access (SPA) deployment. Which statement is true about traffic flows? (Choose two answers)
FortiSASE Secure Private Access (SPA) offers two distinct architectural methods for connecting remote users to private applications: SD-WAN-based SPA and ZTNA-based SPA. Each utilizes a different traffic flow to balance security and performance requirements.
SD-WAN Private Access (Hub-and-Spoke): In this model, the FortiSASE Security Points of Presence (PoPs) act as spokes in a traditional hub-and-spoke VPN topology. When a remote user attempts to access a private network, the traffic is first steered to the closest FortiSASE PoP. The PoP then routes that traffic over a persistent IPsec tunnel to the corporate FortiGate hub (or SPA hub). This ensures that all traffic, regardless of protocol (TCP/UDP), can be inspected by the SASE security stack before entering the private network.
Zero Trust Network Access (ZTNA): Unlike the SD-WAN approach, ZTNA is designed for a 'shortest path' connection. While FortiSASE manages the endpoint's posture and issues certificates, the actual application traffic (the data plane) bypasses the FortiSASE PoP. Instead, the FortiClient agent on the endpoint establishes a direct HTTPS or TCP-forwarding connection to the ZTNA Access Proxy configured on the corporate FortiGate. This significantly reduces latency and is ideal for high-performance TCP-based applications.
According to the FortiSASE 25 Secure Internet Access Architecture Guide, 'In FortiSASE, ZTNA refers to traffic that is destined directly to private resources using the FortiGate ZTNA access proxy traffic flow,' whereas for SD-WAN SPA, the PoPs 'rely on IPsec overlays... to secure and route traffic between PoPs and the networks behind an organization's SD-WAN hubs.'
Refer to the exhibits.
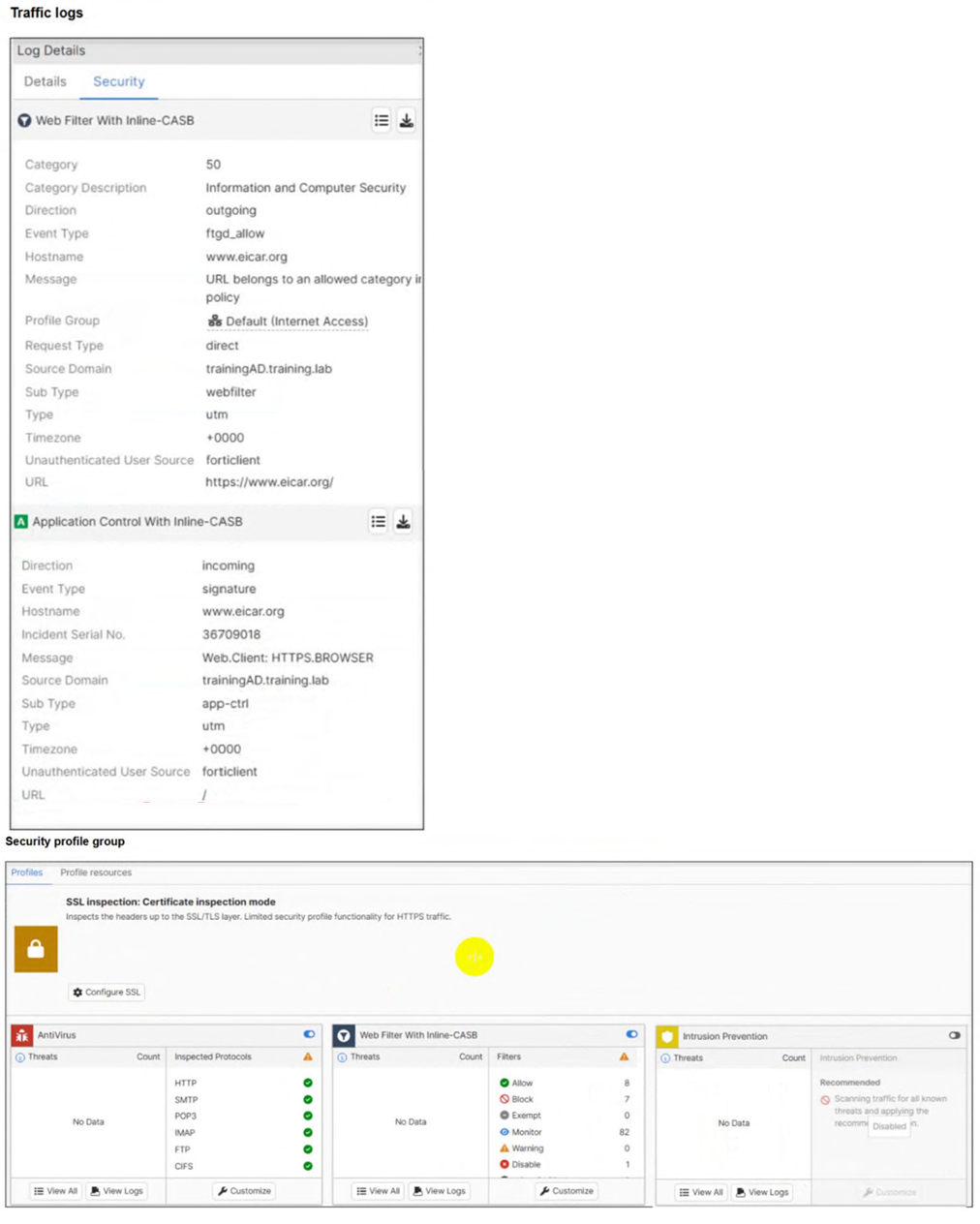
A FortiSASE administrator has configured an antivirus profile in the security profile group and applied it to the internet access policy. Remote users are still able to download the eicar.com-zip file from https://eicar.org.
Which configuration on FortiSASE is allowing users to perform the download? (Choose one answer)
The core of the issue shown in the exhibits is the lack of visibility into encrypted traffic.
HTTPS Encryption: The eicar.org website uses the HTTPS protocol for its downloads. This means the data payload, including the test malware file, is encrypted as it traverses the network.
SSL Inspection Modes: As seen in the Security profile group exhibit (image_5705fc.jpg), the SSL inspection mode is explicitly set to Certificate inspection mode.
Visibility Gap: Certificate inspection only analyzes the initial SSL handshake, such as the server certificate and SNI (Server Name Indication). It does not decrypt the traffic payload. Consequently, the antivirus engine in FortiSASE cannot 'see' or scan the eicar.com-zip file hidden within the encrypted session.
Resolution Requirement: To detect and block malicious files over HTTPS, SSL Deep Inspection must be enabled. Deep inspection allows FortiSASE to act as a proxy, decrypting the traffic for full content scanning by the antivirus and IPS engines before re-encrypting it for the endpoint.
Log Analysis: While the web filtering logs (image_5704e5.jpg) show the traffic is 'Allowed' because the URL is not blocked by a web filter category, this is only the first step of inspection. The antivirus engine is present but ineffective because it is blind to the encrypted content due to the lack of deep inspection.
Unlock All Questions for Fortinet NSE7_SSE_AD-25 Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 81 Questions & Answers