GIAC GCIA Dumps - Pass GIAC Certified Intrusion Analyst v4 Exam in 2026
The GIAC GCIA exam, also known as GIAC Certified Intrusion Analyst v4, is part of the GIAC Cyber Defense certification path. It is designed for professionals who focus on intrusion detection, traffic analysis, and network defense operations. This certification matters for candidates who want to validate practical skills in analyzing network activity and identifying suspicious behavior. Preparing well for this exam can help you build confidence and improve your readiness for real-world security work.
| # | Exam Topics | Sub-Topics | Approximate Weightage (%) |
|---|---|---|---|
| 1 | Advanced IDS Concepts | Detection methods, alert tuning, signature analysis | 12% |
| 2 | Application Protocols | HTTP, DNS, SMTP, protocol behavior | 12% |
| 3 | Concepts of TCP/IP and the Link Layer | Layered communication, packet flow, Ethernet basics | 14% |
| 4 | Fragmentation | IP fragmentation, reassembly, evasion concerns | 10% |
| 5 | IDS Fundamentals and Network Architecture | Sensor placement, network visibility, IDS components | 14% |
| 6 | Intrusion Detection System Rules | Rule structure, thresholds, rule matching | 12% |
| 7 | IP Headers | Header fields, flags, addressing details | 10% |
| 8 | IPv6 | Addressing, extension headers, packet handling | 8% |
| 9 | Network Forensics and Traffic Analysis | Packet review, traffic patterns, evidence interpretation | 8% |
| Total | 100% | ||
This exam tests more than memorization. Candidates must understand network protocols, IDS behavior, packet structure, and traffic analysis at a practical level. It also checks your ability to interpret alerts, identify suspicious patterns, and apply intrusion detection concepts in real environments.
How QA4Exam.com Helps You Pass
QA4Exam.com offers Exam PDF material with actual questions and answers, along with an Online Practice Test built to match the GIAC GCIA exam style. These resources help you study with real exam simulation, so you can get used to the question format and pacing before test day. The content is updated to stay relevant, and the verified answers help you review key concepts with more confidence. You can also practice time management, spot weak areas, and improve your readiness for passing the exam on your first attempt.
Frequently Asked Questions
1. What is the GIAC GCIA exam?
2. Is the GIAC GCIA exam difficult?
3. Can I pass with only braindumps?
4. Do I need hands-on experience for GCIA?
5. Are QA4Exam.com dumps enough to pass in the first attempt?
6. What format do the QA4Exam.com materials use?
7. Is the exam only about memorizing IDS rules?
The questions for GCIA were last updated on Jun 7, 2026.
- Viewing page 1 out of 102 pages.
- Viewing questions 1-5 out of 509 questions
You work as a Network Administrator for Tech Perfect Inc. The office network is configured as an IPv6 network. You have to configure a computer with the IPv6 address, which is equivalent to an IPv4 publicly routable address. Which of the following types of addresses will you choose?
Which of the following malicious programs changes its signature continuously to be invisible to IDS?
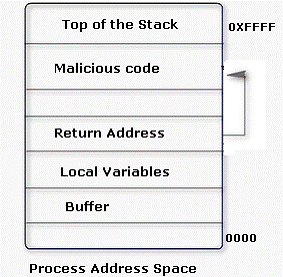
An attacker changes the address of a sub-routine in such a manner that it begins to point to the address of the malicious code. As a result, when the function has been exited, the application can be forced to shift to the malicious code. The image given below explains this phenomenon:
Which of the following tools can be used as a countermeasure to such an attack?
What is the easiest way to verify that name resolution is functioning properly on a TCP/IP network?
Unlock All Questions for GIAC GCIA Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 509 Questions & Answers