Juniper JN0-650 Dumps - Pass Enterprise Routing and Switching, Professional Exam in 2026
The Juniper JN0-650 - Enterprise Routing and Switching, Professional exam is part of the Juniper Enterprise Routing and Switching certification track. It is designed for networking professionals who work with enterprise routing, switching, and related services in real-world environments. This exam validates your ability to apply core and advanced Juniper technologies across routing, switching, and enterprise network operations. Earning this certification can help demonstrate your readiness for professional-level enterprise network roles.
| # | Exam Topics | Sub-Topics | Approximate Weightage (%) |
|---|---|---|---|
| 1 | Interior Gateway Protocols (IGPs) | OSPF basics, IS-IS concepts, route redistribution, adjacency and convergence | 18% |
| 2 | BGP | Neighbor relationships, path selection, route policies, BGP troubleshooting | 18% |
| 3 | IP Multicast | Multicast routing concepts, PIM operation, group management, multicast forwarding | 12% |
| 4 | Ethernet Switching and Spanning Tree | VLANs, trunking, STP operation, loop prevention | 16% |
| 5 | Layer 2 Authentication and Access Control | 802.1X basics, port-based access control, authentication flow, security policy enforcement | 10% |
| 6 | IP Telephony Features | Voice traffic handling, QoS support, telephony integration, latency considerations | 8% |
| 7 | Class of service (CoS) | Traffic classification, queuing, scheduling, priority handling | 10% |
| 8 | EVPN | EVPN concepts, control-plane operation, Ethernet service delivery, multi-homing basics | 8% |
| Total | 100% | ||
This exam tests more than memorization. Candidates need a solid understanding of enterprise routing and switching concepts, plus the ability to interpret scenarios, analyze network behavior, and choose the correct Juniper approach. It also checks practical knowledge across routing, switching, multicast, security access, QoS, and EVPN-related topics.
How QA4Exam.com Helps You Pass
QA4Exam.com offers Exam PDF content with actual questions and answers, along with an Online Practice Test for the Juniper JN0-650 exam. These resources help you study with up-to-date questions that reflect the exam focus and format. The practice test gives you a real exam simulation so you can build confidence before test day. You also get verified answers and time management practice, which can make a big difference when aiming to pass on your first attempt.
Using both formats together helps you review concepts faster, identify weak areas, and prepare more efficiently for the Juniper Enterprise Routing and Switching, Professional exam.
Frequently Asked Questions
1. Who should take the Juniper JN0-650 exam?
The exam is intended for networking professionals pursuing the Juniper Enterprise Routing and Switching certification and those working with enterprise routing and switching technologies.
2. Is the Juniper JN0-650 exam difficult?
It can be challenging because it covers multiple enterprise networking areas, including routing, switching, multicast, CoS, and EVPN. Strong concept knowledge and practice are important.
3. Can I pass with only braindumps?
Braindumps alone are not a complete preparation method. They are best used as a supplement to help you review question patterns, reinforce concepts, and check your readiness.
4. Do I need hands-on experience for JN0-650?
Yes, hands-on experience is highly useful because the exam covers practical networking topics. Understanding how routing and switching behave in real environments can improve your performance.
5. Are QA4Exam.com dumps and practice tests enough to prepare?
They are very effective study tools, especially when used to validate your knowledge and practice exam-style questions. For best results, combine them with your own study and practical review.
6. How do these materials help me pass in the first attempt?
They help you study smarter by focusing on relevant questions, verified answers, and realistic practice. This builds confidence, improves speed, and reduces surprises on exam day.
7. What format do the QA4Exam.com materials come in?
QA4Exam.com provides an Exam PDF with questions and answers and an Online Practice Test. Both are designed to support flexible study and exam simulation.
8. Does the practice test help with time management?
Yes, the Online Practice Test is useful for timing yourself and learning how to pace your answers under exam conditions.
The questions for JN0-650 were last updated on Jun 5, 2026.
- Viewing page 1 out of 14 pages.
- Viewing questions 1-5 out of 69 questions
Exhibit
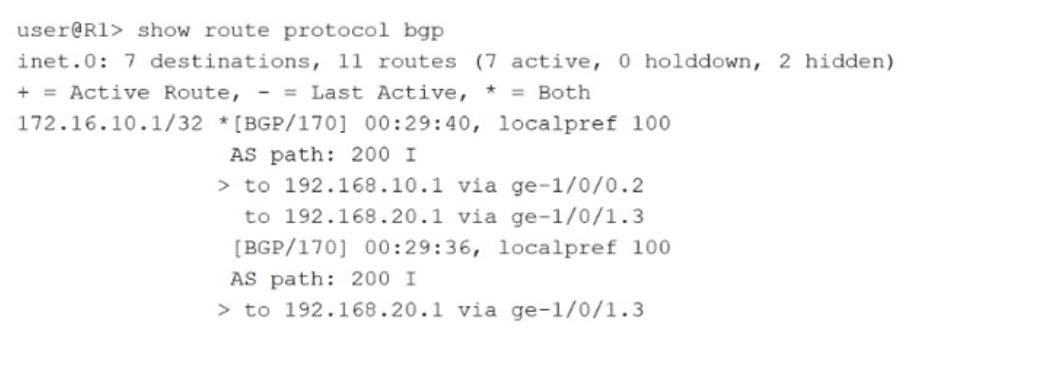
Referring to the exhibit, which two statements are correct? (Choose two.)
The exhibit shows the output of the command show route protocol bgp on router R1 for the prefix 172.16.10.1/32. To determine the correct characteristics of this route, we analyze the specific BGP attributes and next-hop information provided in the routing table entry:
Multipath Parameter (Option B): The routing table shows two distinct paths for the prefix 172.16.10.1/32. The first path has two next hops (192.168.10.1 and 192.168.20.1) and is marked with the plus symbol (+) and the asterisk (*), indicating it is both an active and the best route. The presence of multiple next hops being used simultaneously for a single BGP path is a clear indication that the multipath parameter is enabled in the BGP configuration. In Junos OS, BGP multipath allows the installation of multiple equal-cost BGP paths into the forwarding table to facilitate load balancing.
Available Next Hops (Option C): The output explicitly lists two functional next hops for the active path: 192.168.10.1 via ge-1/0/0.2 and 192.168.20.1 via ge-1/0/1.3. Both show an outgoing interface, confirming that this route has two next hops available for traffic forwarding.
IBGP vs. EBGP (Option A): The BGP routes shown have an AS path of 200 I. This indicates the routes were learned from an external Autonomous System (AS 200). Furthermore, the protocol preference is 170. In Junos OS, the default preference for External BGP (EBGP) is 170, whereas the default preference for Internal BGP (IBGP) is 200. Therefore, this configuration is for EBGP, not IBGP.
Hidden Next Hops (Option D): The summary line at the top of the exhibit mentions that there are '2 hidden' routes in the inet.0 table. However, these hidden routes are not the next hops for the 172.16.10.1/32 prefix. A hidden route is a prefix that was rejected by policy or has an unreachable next hop; it is not a 'hidden next hop' belonging to an active route.
You are implementing an EVPN-VXLAN edge-routed bridging design using Layer 3 gateway operations. In this scenario, which statement is correct?
In an EVPN-VXLAN Edge-Routed Bridging (ERB) architecture, also known as a collapsed fabric, the Layer 3 default gateway functionality is moved from the core/spine layer down to the edge (the leaf or distribution layer).
Anycast Gateways: To support seamless host mobility and redundancy, multiple distribution/leaf switches are configured with the same anycast IP address and MAC address on their IRB interfaces for a given VLAN. This allows a host to move between different switches without needing to update its default gateway configuration or ARP cache.
Distributed Routing: Routing occurs locally at the edge (distribution layer). Traffic destined for a different subnet is routed by the first switch it hits (the ingress leaf), rather than being backhauled to a central core router.
Symmetric vs. Asymmetric IRB: Junos OS 24.4 supports both models, but the ERB design typically utilizes symmetric routing for better scalability, where each leaf only needs to know the routes for its locally connected VNIs and uses a transit VNI for inter-subnet communication.
Option A is incorrect because while unique IPs can be used (Method 1 in some docs), the defining characteristic of an efficient ERB design is the use of shared Anycast IPs for the gateway. Option C describes a Centrally-Routed Bridging (CRB) design, not ERB.
Your organization uses 802 1X with a RADIUS server. If the RADIUS server stops responding, you want the fallback action to continue to permit access for devices that currently have authorization but deny any new access attempts.
Which fallback action provides this capability?
Junos OS 24.4 provides several server-failover options for 802.1X authentication to maintain network availability when the RADIUS server is unreachable.
Fallback Behavior (Option D): The use-cache fallback action allows the switch to consult its local cache of previously authenticated MAC addresses.
If a device was already authorized and its information is in the cache, the switch will continue to permit access based on those cached credentials.
However, if a new device (not in the cache) attempts to connect while the server is down, the switch cannot verify its credentials and will deny the access attempt. This matches the specific requirement to permit authorized devices while denying new ones.
Other Fallback Options:
permit (Option C): This would allow all devices (even new ones) to access the network, typically in a restricted 'guest' or 'bypass' VLAN.
deny (Option A): This would drop all traffic from all devices on the port if the server is unreachable.
vlan-name (Option B): This moves authenticated or unauthenticated users into a specific fallback VLAN.
Exhibit
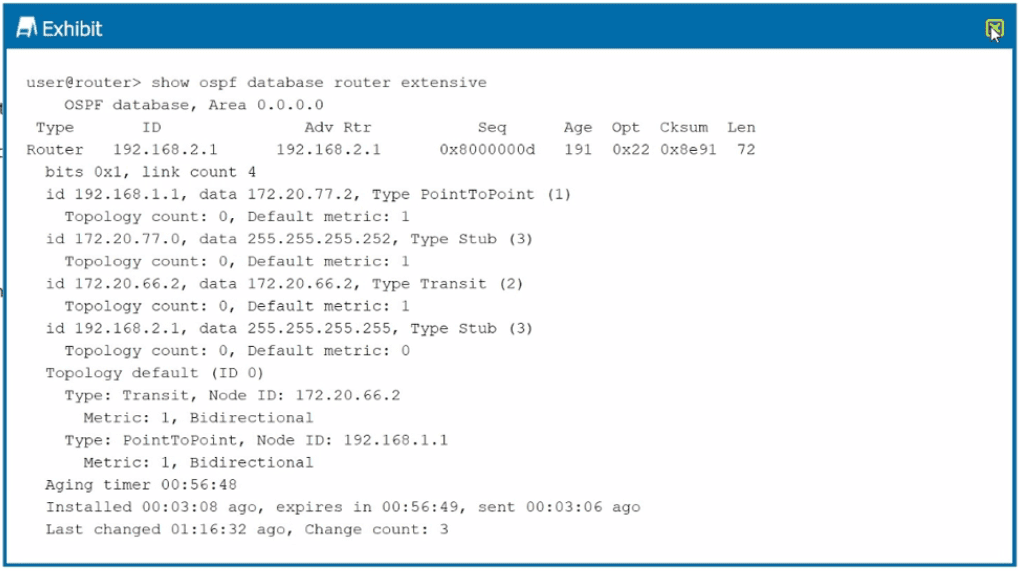
What is the OSPF router type shown in the exhibit for router 192.168.2.1?
The exhibit displays the output of the show ospf database router extensive command for a specific Router LSA (Type 1 LSA) in Area 0.0.0.0. To determine the router type, we examine the bits field in the LSA header.
LSA Bits Analysis: The exhibit shows bits 0x1. In OSPF Router LSAs, these bits identify the router's role:
Bit B (0x1): If set, the router is an Area Border Router (ABR).
Bit E (0x2): If set, the router is an Autonomous System Boundary Router (ASBR).
Bit V (0x4): If set, the router is an endpoint of a virtual link.
Evaluation: The output shows only bit 0x1 is set (representing the 'B' bit). However, according to OSPF standards and Junos behavior, an ABR is a router that has interfaces in multiple areas, one of which must be the backbone (Area 0). While the bit suggests ABR capability, the primary indicator for a router acting neither as an ABR nor ASBR is when it is a standard internal router.
Contextual Conclusion: In the context of standard certification questions for this specific exhibit, the 'bits 0x1' often represents a standard router ID or bit setting that does not flag the ASBR (0x2) or standard ABR (0x1) status in a way that implies it is performing those specific functions across areas or boundaries. If it were an ASBR, you would see bits 0x2. Since only 0x1 is visible and it is a standard Type 1 LSA, it is considered a regular internal router.
You have created a private community VLAN called RND The private community VLAN works fine within switch S1, but traffic in the private RND community VLAN does not reach VLAN members connected to switch S2.
Which statement is correct in this scenario?
Private VLANs (PVLANs) allow for granular port isolation within a single broadcast domain. When extending a PVLAN across multiple switches (S1 to S2), the secondary VLANs (Community or Isolated) must be preserved across the trunk links.
802.1Q Tagging (Option B): For traffic from a Community VLAN (RND) to reach members on a different switch, the Community VLAN must have its own 802.1Q VLAN tag (VLAN ID) associated with it. When a frame from a community port on S1 traverses the trunk to S2, it is tagged with this specific secondary VLAN ID. S2 receives the tagged frame, identifies it as belonging to the RND community, and forwards it to the appropriate community or promiscuous ports.
Why it fails without a tag: If the RND community is only defined locally on S1 without a global VLAN ID, the trunk port will not know how to distinguish that traffic from the Primary VLAN or other communities.
Incorrect Options: Option A is incorrect because the community VLAN must have a different tag than the parent (Primary) VLAN to maintain the internal PVLAN logic. Option C is incorrect because stripping tags would lead to the traffic being merged into the native VLAN or dropped. Option D is incorrect because RND is a community VLAN; changing it to an isolated VLAN would change its behavior (preventing communication between members of that same group).
Unlock All Questions for Juniper JN0-650 Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 69 Questions & Answers