Linux Foundation CKA Dumps - Pass Certified Kubernetes Administrator Exam in 2026
The Linux Foundation CKA, or Certified Kubernetes Administrator exam, is a respected certification for professionals who work with Kubernetes in real-world environments. It belongs to the Kubernetes Administrator certification track and is designed for candidates who manage, configure, and troubleshoot Kubernetes clusters. This exam matters because it validates practical skills that are directly relevant to modern cloud-native operations and platform administration.
Exam Topics and Approximate Weightage
| # | Exam Topics | Sub-Topics | Approximate Weightage (%) |
|---|---|---|---|
| 1 | Cluster Architecture, Installation & Configuration | Cluster components, control plane setup, node configuration, cluster bootstrapping | 25% |
| 2 | Workloads & Scheduling | Pods, deployments, daemonsets, jobs, scheduling constraints | 20% |
| 3 | Services & Networking | Services, ingress, network policies, DNS, service exposure | 20% |
| 4 | Storage | Persistent volumes, persistent volume claims, storage classes, volume mounting | 15% |
| 5 | Troubleshooting | Cluster issues, application failures, logs, events, node and pod diagnostics | 20% |
The exam tests your ability to perform Kubernetes administration tasks in a hands-on environment, not just recall theory. Candidates need a solid understanding of cluster operations, workload management, networking, storage, and troubleshooting. Success depends on practical skill, command-line confidence, and the ability to complete tasks accurately under time pressure.
How QA4Exam.com Helps You Pass
QA4Exam.com offers CKA Exam PDF materials with actual questions and answers, plus an Online Practice Test that helps you prepare with confidence. These resources are built to simulate the real exam experience so you can get familiar with the question style and improve your speed. The content is updated to stay relevant, and the verified answers help you study with more accuracy. By practicing with timed questions, you can build better time management skills and be more prepared to pass the Linux Foundation CKA exam on your first attempt.
Frequently Asked Questions
1. Who should take the Linux Foundation CKA exam?
The CKA exam is intended for professionals who want to validate their Kubernetes administration skills, especially those working with cluster setup, operations, and troubleshooting.
2. Is the CKA exam difficult?
Yes, it can be challenging because it focuses on practical tasks and time management. Candidates usually need hands-on Kubernetes experience to feel confident.
3. Can I pass CKA with only braindumps?
Braindumps alone are not a complete preparation method. You should also understand the concepts and practice the tasks so you can handle the exam environment effectively.
4. Do I need hands-on experience before taking CKA?
Yes, hands-on experience is highly recommended because the exam measures real administration skills across cluster architecture, workloads, networking, storage, and troubleshooting.
5. Are the QA4Exam.com dumps and practice test enough for first-attempt success?
They can be a strong part of your preparation because they provide real exam-style questions, verified answers, and practice for managing time, but you should still review the exam topics carefully.
6. What is included in the QA4Exam.com CKA exam PDF and online practice test?
The CKA exam PDF includes actual questions and answers, while the online practice test helps you simulate the exam and check your readiness before test day.
7. How does practice testing help with passing CKA on the first attempt?
Practice testing helps you improve speed, identify weak areas, and become comfortable with the exam format, which can increase your chances of passing on the first attempt.
The questions for CKA were last updated on Jun 6, 2026.
- Viewing page 1 out of 17 pages.
- Viewing questions 1-5 out of 83 questions
SIMULATION
Task Weight: 4%
Task
Schedule a Pod as follows:
* Name: kucc1
* App Containers: 2
* Container Name/Images:
o nginx
o consul
Solution:



SIMULATION
Create a nginx pod with label env=test in engineering namespace
kubectl run nginx --image=nginx --restart=Never --labels=env=test --namespace=engineering --dry-run -o yaml > nginx-pod.yaml
kubectl run nginx --image=nginx --restart=Never --labels=env=test --namespace=engineering --dry-run -o yaml | kubectl create -n engineering -f --
YAML File:
apiVersion: v1
kind: Pod
metadata:
name: nginx
namespace: engineering
labels:
env: test
spec:
containers:
- name: nginx
image: nginx
imagePullPolicy: IfNotPresent
restartPolicy: Never
kubectl create -f nginx-pod.yaml
SIMULATION
Create a deployment spec file that will:
Launch 7 replicas of the nginx Image with the labelapp_runtime_stage=dev
deployment name: kual00201
Save a copy of this spec file to /opt/KUAL00201/spec_deployment.yaml
(or /opt/KUAL00201/spec_deployment.json).
When you are done, clean up (delete) any new Kubernetes API object that you produced during this task.
solution


SIMULATION
Create an nginx pod and list the pod with different levels of verbosity
// create a pod
kubectl run nginx --image=nginx --restart=Never --port=80
// List the pod with different verbosity
kubectl get po nginx --v=7
kubectl get po nginx --v=8
kubectl get po nginx --v=9
SIMULATION
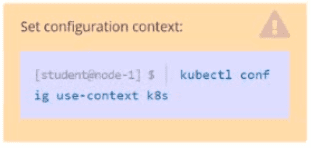
Configure the kubelet systemd- managed service, on the node labelled with name=wk8s-node-1, to launch a pod containing a single container of Image httpd named webtool automatically. Any spec files required should be placed in the /etc/kubernetes/manifests directory on the node.
You can ssh to the appropriate node using:
[student@node-1] $ ssh wk8s-node-1
You can assume elevated privileges on the node with the following command:
[student@wk8s-node-1] $ | sudo --i
solution





Unlock All Questions for Linux Foundation CKA Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 83 Questions & Answers