Linux Foundation CKS Dumps - Pass Certified Kubernetes Security Specialist Exam in 2026
The Linux Foundation CKS, or Certified Kubernetes Security Specialist, is a focused certification in the Kubernetes Security Specialist track. It is designed for professionals who work with Kubernetes and want to validate practical security skills across cluster and workload protection. This exam matters because it confirms your ability to secure Kubernetes environments in real-world scenarios. For administrators, engineers, and security-focused DevOps professionals, CKS is a strong proof of hands-on security knowledge.
Exam Topics
| # | Exam Topics | Sub-Topics | Approximate Weightage (%) |
|---|---|---|---|
| 1 | Cluster Setup | Cluster access controls, secure baseline configuration, namespace isolation | 15% |
| 2 | Cluster Hardening | API server hardening, RBAC review, admission control configuration | 20% |
| 3 | System Hardening | Host security settings, Linux kernel protection, secure runtime permissions | 15% |
| 4 | Minimize Microservice Vulnerabilities | Least privilege access, container security context, pod security controls | 20% |
| 5 | Supply Chain Security | Image verification, trusted registries, vulnerability scanning | 15% |
| 6 | Monitoring, Logging and Runtime Security | Threat detection, audit logging, runtime behavior monitoring | 15% |
The CKS exam tests practical Kubernetes security skills, not just theory. Candidates must understand how to secure clusters, reduce application risk, and respond to runtime threats under time pressure. The exam expects strong hands-on ability, good command of Kubernetes security concepts, and the confidence to solve tasks quickly and accurately.
How QA4Exam.com Helps You Pass
QA4Exam.com offers CKS Exam PDF materials with actual questions and answers, plus an Online Practice Test to strengthen your preparation. The practice test gives you a real exam simulation so you can get used to the format, pacing, and pressure of the Linux Foundation CKS exam. You also benefit from up-to-date questions and verified answers that help you focus on the right topics with confidence. With repeated practice, you can improve time management and increase your chances of passing the Certified Kubernetes Security Specialist exam on your first attempt.
Frequently Asked Questions
CKS stands for Certified Kubernetes Security Specialist. It is a Linux Foundation certification that validates practical Kubernetes security skills for professionals who work with secure cluster and workload operations.
The exam is ideal for Kubernetes administrators, DevOps engineers, cloud engineers, and security-focused professionals who want to validate hands-on security knowledge in Kubernetes environments.
Yes, it is considered challenging because it focuses on practical tasks and secure configuration under time constraints. Strong hands-on experience with Kubernetes security concepts is important for success.
Braindumps alone are not a safe strategy. You should use QA4Exam.com dumps and practice tests as a preparation aid, but hands-on understanding and repeated practice are still important for passing the exam.
Yes, hands-on experience is highly recommended. The exam is practical, so being able to work through security tasks quickly and accurately is a major advantage.
The PDF questions and answers help you review likely exam content, while the online practice test helps you simulate the real exam and improve speed. Together, they build familiarity, confidence, and better time management for the first attempt.
QA4Exam.com provides verified answers and up-to-date questions so you can study with more confidence and focus on relevant CKS exam objectives.
The CKS preparation package includes an Exam PDF with questions and answers and an Online Practice Test designed to mirror exam-style preparation and improve your readiness.
The questions for CKS were last updated on Jun 5, 2026.
- Viewing page 1 out of 13 pages.
- Viewing questions 1-5 out of 64 questions
SIMULATION
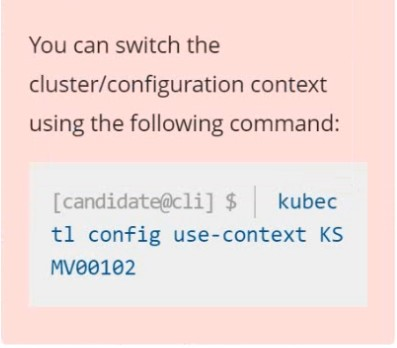
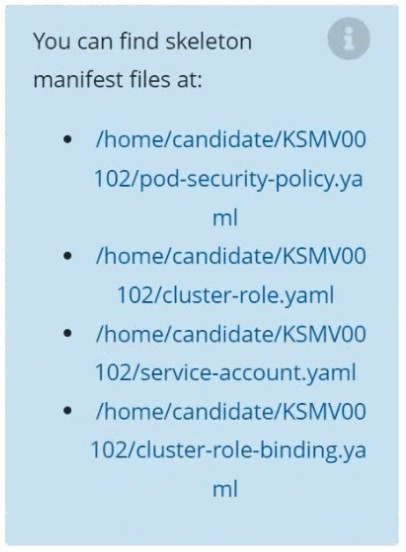
Context
A PodSecurityPolicy shall prevent the creation of privileged Pods in a specific namespace.
Task
Create a new PodSecurityPolicy named prevent-psp-policy,which prevents the creation of privileged Pods.
Create a new ClusterRole named restrict-access-role, which uses the newly created PodSecurityPolicy prevent-psp-policy.
Create a new ServiceAccount named psp-restrict-sa in the existing namespace staging.
Finally, create a new ClusterRoleBinding named restrict-access-bind, which binds the newly created ClusterRole restrict-access-role to the newly created ServiceAccount psp-restrict-sa.













SIMULATION
Documentation dockerd
You must connect to the correct host . Failure to do so may result in a zero score.
[candidate@base] $ ssh cks000037
Task
Perform the following tasks to secure the cluster node cks000037 :
Remove user developer from the docker group.
Do not remove the user from any other group.
Reconfigure and restart the Docker daemon to ensure that the socket
file located at /var/run/docker.sock is owned by the group root.
Re-configure and restart the Docker daemon to ensure it does not listen on any TCP port.
After completing your work, ensure the Kubernetes cluster is healthy.
1) Connect to the correct host
ssh cks000037
sudo -i
2) Remove user developer from the docker group ONLY
2.1 Verify current groups (optional but fast)
id developer
2.2 Remove ONLY from docker group
gpasswd -d developer docker
2.3 Verify removal
id developer
docker should not appear; other groups must remain.
3) Reconfigure Docker to secure the socket and disable TCP
Docker config file:
vi /etc/docker/daemon.json
3.1 Set socket group to root and disable TCP listeners
Ensure the file contains exactly these relevant settings (merge with existing JSON if present):
{
'group': 'root',
'hosts': ['unix:///var/run/docker.sock']
}
Important:
'group': 'root' docker.sock owned by group root
'hosts' includes ONLY the unix socket (no tcp://)
If the file already exists with other keys, add/adjust only these keys and keep valid JSON (commas!).
Save and exit:
:wq
4) Restart Docker daemon
systemctl daemon-reload
systemctl restart docker
systemctl status docker --no-pager
5) Verify Docker socket ownership and permissions
ls -l /var/run/docker.sock
Expected:
srw-rw---- 1 root root ...
Owner: root
Group: root
6) Verify Docker is NOT listening on TCP
ss -lntp | grep docker
Expected:
No output (or nothing bound to TCP by dockerd)
Optional double-check:
ps aux | grep dockerd | grep -v grep
Ensure no -H tcp://... flags.
7) Ensure Kubernetes cluster is healthy
7.1 Check node and pods
export KUBECONFIG=/etc/kubernetes/admin.conf
kubectl get nodes
kubectl get pods -A
All nodes should be Ready, core pods Running.
SIMULATION
Create a PSP that will only allow the persistentvolumeclaim as the volume type in the namespace restricted.
Create a new PodSecurityPolicy named prevent-volume-policy which prevents the pods which is having different volumes mount apart from persistentvolumeclaim.
Create a new ServiceAccount named psp-sa in the namespace restricted.
Create a new ClusterRole named psp-role, which uses the newly created Pod Security Policy prevent-volume-policy
Create a new ClusterRoleBinding named psp-role-binding, which binds the created ClusterRole psp-role to the created SA psp-sa.
Hint:
Also, Check the Configuration is working or not by trying to Mount a Secret in the pod maifest, it should get failed.
POD Manifest:
apiVersion: v1
kind: Pod
metadata:
name:
spec:
containers:
- name:
image:
volumeMounts:
- name:
mountPath:
volumes:
- name:
secret:
secretName:
apiVersion: policy/v1beta1
kind: PodSecurityPolicy
metadata:
name: restricted
annotations:
seccomp.security.alpha.kubernetes.io/allowedProfileNames: 'docker/default,runtime/default'
apparmor.security.beta.kubernetes.io/allowedProfileNames: 'runtime/default'
seccomp.security.alpha.kubernetes.io/defaultProfileName: 'runtime/default'
apparmor.security.beta.kubernetes.io/defaultProfileName: 'runtime/default'
spec:
privileged: false
# Required to prevent escalations to root.
allowPrivilegeEscalation: false
# This is redundant with non-root + disallow privilege escalation,
# but we can provide it for defense in depth.
requiredDropCapabilities:
- ALL
# Allow core volume types.
volumes:
- 'configMap'
- 'emptyDir'
- 'projected'
- 'secret'
- 'downwardAPI'
# Assume that persistentVolumes set up by the cluster admin are safe to use.
- 'persistentVolumeClaim'
hostNetwork: false
hostIPC: false
hostPID: false
runAsUser:
# Require the container to run without root privileges.
rule: 'MustRunAsNonRoot'
seLinux:
# This policy assumes the nodes are using AppArmor rather than SELinux.
rule: 'RunAsAny'
supplementalGroups:
rule: 'MustRunAs'
ranges:
# Forbid adding the root group.
- min: 1
max: 65535
fsGroup:
rule: 'MustRunAs'
ranges:
# Forbid adding the root group.
- min: 1
max: 65535
readOnlyRootFilesystem: false
SIMULATION
Context
You must fully integrate a container image scanner into the kubeadm provisioned cluster.
Task
Given an incomplete configuration located at /etc/kubernetes/bouncer and a functional container image scanner
with an HTTPS endpoint at https://smooth-yak.local/review, perform the following tasks to implement a validating admission controller.
First, re-configure the API server to enable all admission plugin(s) to support the provided AdmissionConfiguration.
Next, re-configure the ImagePolicyWebhook configuration to deny images on backend failure.
Next, complete the backend configuration to point to the container image scanner's endpoint at https://smooth-yak.local/review.
Finally, to test the configuration, deploy the test resource defined in /home/candidate/vulnerable.yaml which is using an image that should be denied.
You may delete and re-create the resource as often as needed.
The container image scanner's log file is located at /var/log/nginx/access_log.
Below is the CKS exam style ''do-this-exactly'' runbook for Q3. It includes the minimal discovery commands (so you don't guess filenames), then the exact lines/blocks to set.
QUESTION 3 -- ImagePolicyWebhook (Validating Admission) -- Exam Steps
0) SSH + root
ssh cks000002
sudo -i
1) Identify the provided config files (no guessing)
ls -la /etc/kubernetes/bouncer
You are looking for files typically named like:
admission_configuration.yaml (AdmissionConfiguration)
imagepolicywebhook.yaml (ImagePolicyWebhookConfiguration) OR the ImagePolicyWebhook config embedded inside the AdmissionConfiguration
kubeconfig (webhook kubeconfig)
If unsure which is which, quick peek:
grep -R 'ImagePolicyWebhook' -n /etc/kubernetes/bouncer
grep -R 'AdmissionConfiguration' -n /etc/kubernetes/bouncer
grep -R 'kubeconfig' -n /etc/kubernetes/bouncer
PART A --- Reconfigure API Server to enable required admission plugin(s)
2) Edit API server static pod manifest
vi /etc/kubernetes/manifests/kube-apiserver.yaml
2.1 Enable the admission plugin ImagePolicyWebhook
Find the line starting with:
- --enable-admission-plugins=
Ensure ImagePolicyWebhook is included in that comma list.
Example (your list may differ; just add ImagePolicyWebhook):
- --enable-admission-plugins=NodeRestriction,ImagePolicyWebhook
If the flag does not exist, add one line under command::
- --enable-admission-plugins=ImagePolicyWebhook
2.2 Point API server to the provided AdmissionConfiguration
In the same file, ensure this flag exists (use the file in /etc/kubernetes/bouncer that contains AdmissionConfiguration):
- --admission-control-config-file=/etc/kubernetes/bouncer/admission_configuration.yaml
If your file is named differently, use the real filename you found in step 1, but keep the flag name exactly --admission-control-config-file.
Save/exit:
:wq
Static pod will restart automatically (kubelet watches the manifest).
Optional quick watch:
docker ps | grep kube-apiserver
# or:
crictl ps | grep kube-apiserver
PART B --- Configure ImagePolicyWebhook to deny images on backend failure
3) Edit the ImagePolicyWebhook config
One of these is true on your cluster:
Option 1 (most common in these tasks): ImagePolicyWebhook config is a standalone file
Edit the file in /etc/kubernetes/bouncer that contains kind: ImagePolicyWebhookConfiguration:
grep -R 'kind: ImagePolicyWebhookConfiguration' -n /etc/kubernetes/bouncer
vi /etc/kubernetes/bouncer/<THE_FILE_YOU_FOUND>.yaml
Set (or ensure) exactly:
defaultAllow: false
Option 2: ImagePolicyWebhook config is embedded inside AdmissionConfiguration
Edit the AdmissionConfiguration file:
vi /etc/kubernetes/bouncer/admission_configuration.yaml
Find the plugin section for ImagePolicyWebhook and ensure the config includes:
defaultAllow: false
Save/exit:
:wq
PART C --- Point backend configuration to https://smooth-yak.local/review
4) Edit the webhook kubeconfig to use the scanner endpoint
Find the kubeconfig file referenced by the ImagePolicyWebhook config.
Search for kubeConfigFile:
grep -R 'kubeConfigFile' -n /etc/kubernetes/bouncer
Open that kubeconfig path (example name below; yours may differ):
vi /etc/kubernetes/bouncer/kubeconfig
In kubeconfig, set the cluster server exactly:
clusters:
- cluster:
server: https://smooth-yak.local/review
Save/exit:
:wq
PART D --- Restart effect (make sure API server picks up config)
Because you already edited /etc/kubernetes/manifests/kube-apiserver.yaml, the API server restarted.
To be safe (and fast), force a restart by ''touching'' the manifest (no content change needed):
touch /etc/kubernetes/manifests/kube-apiserver.yaml
PART E --- Test: apply vulnerable workload and confirm it is denied
5) Use admin kubeconfig (because old kubectl config may break)
export KUBECONFIG=/etc/kubernetes/admin.conf
kubectl get nodes
6) Deploy the test resource (should be DENIED)
kubectl apply -f /home/candidate/vulnerable.yaml
Expected: admission error/denied message.
If it already exists:
kubectl delete -f /home/candidate/vulnerable.yaml
kubectl apply -f /home/candidate/vulnerable.yaml
PART F --- Verify the scanner was called (log check)
7) Check scanner access log
tail -n 50 /var/log/nginx/access_log
You should see requests hitting /review.
Quick ''what to check if it doesn't deny''
Run these in order:
Confirm API server flags:
grep -n 'enable-admission-plugins' /etc/kubernetes/manifests/kube-apiserver.yaml
grep -n 'admission-control-config-file' /etc/kubernetes/manifests/kube-apiserver.yaml
Confirm deny-on-failure:
grep -R 'defaultAllow' -n /etc/kubernetes/bouncer
Must show:
defaultAllow: false
Confirm endpoint:
grep -R 'server: https://smooth-yak.local/review' -n /etc/kubernetes/bouncer
API server logs (docker runtime):
docker ps | grep kube-apiserver
docker logs $(docker ps -q --filter name=kube-apiserver) --tail 80
If you paste the output of:
ls - /etc/kubernetes/bouncer
grep -R 'kind: AdmissionConfiguration' -n /etc/kubernetes/bouncer
grep -R 'ImagePolicyWebhook' -n /etc/kubernetes/bouncer
SIMULATION
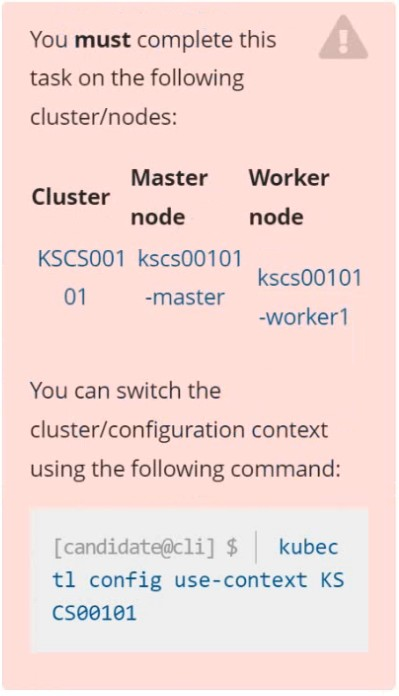
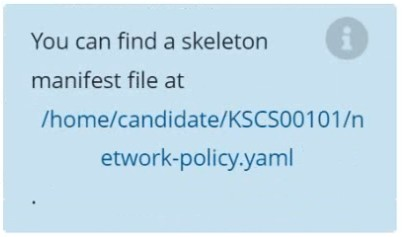
Context
A default-deny NetworkPolicy avoids to accidentally expose a Pod in a namespace that doesn't have any other NetworkPolicy defined.
Task
Create a new default-deny NetworkPolicy named defaultdeny in the namespace testing for all traffic of type Egress.
The new NetworkPolicy must deny all Egress traffic in the namespace testing.
Apply the newly created default-deny NetworkPolicy to all Pods running in namespace testing.



Unlock All Questions for Linux Foundation CKS Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 64 Questions & Answers