Microsoft AZ-104 Dumps - Pass Microsoft Azure Administrator Exam in First Attempt 2026
The Microsoft AZ-104 Microsoft Azure Administrator Exam is part of the Azure Administrator Associate certification track. It is designed for IT professionals who manage Azure services, including networking, compute, identity, governance, storage, and monitoring. This exam matters for candidates who want to validate practical cloud administration skills and prove they can handle day-to-day Azure operations.
Exam Topics and Approximate Weightage
| # | Exam Topics | Sub-Topics | Approximate Weightage (%) |
|---|---|---|---|
| 1 | Implement and manage virtual networking | Virtual networks and subnets; Network security groups; DNS and routing; Private access and connectivity | 25% |
| 2 | Deploy and manage Azure compute resources | Virtual machines; VM availability and scaling; App Service basics; Container and compute deployment | 20% |
| 3 | Manage Azure identities and governance | Microsoft Entra ID users and groups; Role-based access control; Subscriptions and management groups; Policy and locks | 20% |
| 4 | Implement and manage storage | Storage accounts; Blobs, files, queues, and tables; Access tiers and replication; Storage security and access control | 20% |
| 5 | Monitor and maintain Azure resources | Azure Monitor; Alerts and metrics; Log Analytics and diagnostics; Backup and resource health | 15% |
This exam tests more than memorization. Candidates must show practical knowledge of Azure administration, understand how services work together, and apply the right configuration choices in real scenarios. It also checks your ability to solve operational tasks efficiently and maintain secure, reliable cloud resources.
How QA4Exam.com Helps You Pass
QA4Exam.com offers an Exam PDF with actual questions and answers plus an Online Practice Test for the Microsoft AZ-104 exam. These materials help you study with real exam simulation, so you can get familiar with the question style and pressure before test day.
The questions are updated to stay relevant, and the verified answers help you check your understanding quickly. The practice test also supports time management practice, which is important when you want to finish confidently and pass on your first attempt.
With focused preparation and repeated practice, you can strengthen weak areas and improve your readiness for the Microsoft Azure Administrator Exam.
Frequently Asked Questions
1. Who should take the Microsoft AZ-104 exam?
The exam is for IT professionals who want to validate their ability to manage Azure resources and earn the Azure Administrator Associate certification.
2. Is the Microsoft Azure Administrator Exam difficult?
It can be challenging because it tests practical Azure administration skills across networking, compute, identity, storage, and monitoring.
3. Can I pass with only braindumps?
Braindumps alone are not the best approach. You should use them with practice and hands-on understanding to improve your chances of passing.
4. Do I need hands-on experience for AZ-104?
Hands-on experience is strongly recommended because the exam focuses on real administrative tasks and practical Azure decision-making.
5. Are QA4Exam.com dumps enough to prepare for the exam?
QA4Exam.com dumps are useful for question practice and answer review, but combining them with broader study and practice is the most effective way to prepare.
6. How does the QA4Exam.com practice test help with first-attempt success?
The Online Practice Test helps you simulate the exam, manage time, review verified answers, and identify weak areas before the real test.
7. What format do the QA4Exam.com materials come in?
QA4Exam.com provides an Exam PDF with questions and answers and an Online Practice Test for interactive preparation.
The questions for AZ-104 were last updated on Jun 6, 2026.
- Viewing page 1 out of 86 pages.
- Viewing questions 1-5 out of 429 questions
You have an Azure subscription that contains The storage accounts shown in the following table.
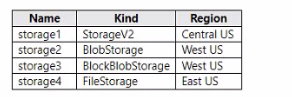
You deploy a web app named Appl to the West US Azure region.
You need to back up Appl. The solution must minimize costs.
Which storage account should you use as the target for the backup?
To back up a web app, you need to configure a custom backup that specifies a storage account and a container as the target for the backup1.The storage account must be in the same subscription as the web app, and the container must be accessible by the web app2. The backup size is limited to 10 GB, and the backup frequency can be configured to minimize costs.
According to the table, storage1 is the only storage account that meets these requirements. Storage1 is in the same subscription and region as the web app, and it is a general-purpose v2 account that supports custom backups. Storage2 and storage3 are in a different region than the web app, which may incur additional costs for data transfer. Storage4 is a FilesStorage account, which does not support custom backups.
Therefore, you should use storage1 as the target for the backup of your web app. To configure a custom backup, you can follow these steps:
In your app management page in the Azure portal, in the left menu, select Backups.
At the top of the Backups page, select Configure custom backups.
In Storage account, select storage1. Do the same with Container.
Specify the backup frequency, retention period, and database settings as needed.
Click Configure.
At the top of the Backups page, select Backup Now.
You have an Azure subscription that contains multiple virtual machines in the West US Azure region.
You need to use Traffic Analytics in Azure Network Watcher to monitor virtual machine traffic.
Which two resources should you create? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
Traffic Analytics is a feature within Azure Network Watcher that provides insights into network traffic patterns, security threats, and performance using NSG flow logs. To enable Traffic Analytics, two key resources are required:
A Log Analytics Workspace -- This is where Azure Network Watcher sends and stores the processed flow log data for analysis.
A Storage Account -- Network Security Group (NSG) flow logs are first written to a designated storage account before they are ingested by Traffic Analytics for processing.
According to Microsoft Azure Administrator documentation, under ''Enable Traffic Analytics'':
''Traffic Analytics uses Network Watcher NSG flow logs, which must be stored in a storage account. These logs are then processed and analyzed in a Log Analytics workspace to provide insights into network activity.''
Workflow:
NSG flow logs stored in Azure Storage Account
Logs are processed by Azure Monitor ingested into Log Analytics workspace
Traffic Analytics visualizes and analyzes the data
Other options such as Azure Monitor workbooks or Sentinel workspaces are not mandatory to activate Traffic Analytics.
Thus, to use Traffic Analytics, you must create: A Storage Account to store flow logs A Log Analytics Workspace to process and visualize them
You have an Azure virtual machine named VM1. VM1 was deployed by using a custom Azure Resource Manager template named ARMIjson.
You receive a notification that VM1 will be affected by maintenance.
You need to move VM1 to a different host immediately.
Solution: From the VM1 Redeploy + reapply blade, you select Redeploy.
Does this meet the goal?
When Microsoft schedules maintenance that may affect a virtual machine (VM), administrators have two options:
Wait for Azure to perform the maintenance automatically.
Move the VM to a new host proactively to minimize or avoid downtime.
According to the Microsoft Azure Administrator documentation, using the ''Redeploy + reapply'' option in the Azure portal forces the VM to migrate to a new Azure host within the same region and availability set.
Here's what happens when you click Redeploy:
Azure shuts down the existing VM.
The VM is moved to a new physical host within the same region.
The operating system disk and data disks are retained, and network configuration (NICs, public IP, etc.) is preserved.
Once redeployed, Azure reassigns the VM to the same virtual network and reattaches disks and configurations.
This method is explicitly recommended by Microsoft to proactively address maintenance events or host-related issues like ''unresponsive VM'' or ''performance degradation.''
Therefore, using the Redeploy operation from the ''Redeploy + reapply'' blade effectively achieves the goal of moving the VM to a different host immediately.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You need to ensure that an Azure Active Directory (Azure AD) user named Admin1 is assigned the required role to enable Traffic Analytics for an Azure subscription.
Solution: You assign the Traffic Manager Contributor role at the subscription level to Admin1
The Traffic Manager Contributor role is not related to Traffic Analytics. Traffic Manager is a service that provides DNS-based load balancing and traffic routing across different regions and endpoints.Traffic Manager Contributor is a role that allows you to create and manage Traffic Manager profiles, endpoints, and geographies1.
Traffic Analytics is a service that provides visibility into user and application activity in your cloud networks. Traffic Analytics analyzes Azure Network Watcher network security group (NSG) flow logs to provide insights into traffic flow in your Azure cloud.With Traffic Analytics, you can visualize network activity, identify hot spots, secure your network, optimize your network deployment, and pinpoint network misconfigurations2.
To enable Traffic Analytics for an Azure subscription, you need to have a role that grants you the following permissions at the subscription level:
Microsoft.Network/applicationGateways/read
Microsoft.Network/connections/read
Microsoft.Network/loadBalancers/read
Microsoft.Network/localNetworkGateways/read
Microsoft.Network/networkInterfaces/read
Microsoft.Network/networkSecurityGroups/read
Microsoft.Network/publicIPAddresses/read
Microsoft.Network/routeTables/read
Microsoft.Network/virtualNetworkGateways/read
Microsoft.Network/virtualNetworks/read
Microsoft.OperationalInsights/workspaces/*
Some of the built-in roles that have these permissions are Owner, Contributor, or Network Contributor3. However, these roles also grant other permissions that may not be necessary or desirable for enabling Traffic Analytics.Therefore, the best practice is to use the principle of least privilege and create a custom role that only has the required permissions for enabling Traffic Analytics4.
Therefore, to meet the goal of ensuring that an Azure AD user named Admin1 is assigned the required role to enable Traffic Analytics for an Azure subscription, you should create a custom role with the required permissions and assign it to Admin1 at the subscription level.
You are planning the move of App1 to Azure.
You create a network security group (NSG).
You need to recommend a solution to provide users with access to App1.
What should you recommend?
As App1 is public-facing we need an incoming security rule, related to the access of the web servers.
Scenario: You have a public-facing application named App1. App1 is comprised of the following three tiers: a SQL database, a web front end, and a processing middle tier.
Each tier is comprised of five virtual machines. Users access the web front end by using HTTPS only.
Unlock All Questions for Microsoft AZ-104 Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 429 Questions & Answers