Netskope NSK101 Dumps - Pass the Netskope Certified Cloud Security Administrator Exam in First Attempt 2026
The Netskope NSK101 - Netskope Certified Cloud Security Administrator Exam is part of the Netskope Cloud Security Certification Program. It is designed for candidates who want to validate their knowledge of Netskope cloud security administration, platform management, and monitoring concepts. This certification matters for professionals responsible for securing cloud networks and operating the Netskope platform effectively. Earning this credential helps demonstrate practical understanding of cloud security operations in real-world environments.
| # | Exam Topics | Sub-Topics | Approximate Weightage (%) |
|---|---|---|---|
| 1 | Security Concepts for Cloud Networks | Cloud security principles, threat prevention, policy basics, secure access concepts | 20% |
| 2 | Foundational Concepts of Netskope Platform | Platform architecture, core components, deployment overview, key terminology | 20% |
| 3 | Management of Netskope Platform | Administrative settings, policy management, user and role controls, configuration tasks | 22% |
| 4 | Overseeing and checking the Netskope platform | Monitoring dashboards, alerts, logs, activity review, operational visibility | 18% |
| 5 | Maintenance of Netskope Platform | Routine maintenance, updates, troubleshooting, platform health checks | 20% |
| Total | 100% | ||
This exam tests both conceptual understanding and practical administration skills related to the Netskope platform. Candidates should expect questions on cloud security fundamentals, platform setup, management workflows, monitoring, and maintenance activities. Success depends on knowing how the platform works and how to apply that knowledge in administrative scenarios.
How QA4Exam.com Helps You Pass
QA4Exam.com offers the NSK101 Exam PDF with actual questions and answers, along with an Online Practice Test designed to match the exam style. These resources help you experience a realistic exam simulation, review up-to-date questions, and verify answers before test day. The practice test also improves your time management by helping you answer questions under exam-like pressure. With focused preparation and repeated practice, you can build confidence and aim to pass the Netskope NSK101 exam on your first attempt.
Frequently Asked Questions
1. What is the Netskope NSK101 exam?
The NSK101 exam is the Netskope Certified Cloud Security Administrator Exam and belongs to the Netskope Cloud Security Certification Program. It focuses on cloud security concepts, Netskope platform fundamentals, management, monitoring, and maintenance.
2. Who should take the Netskope Certified Cloud Security Administrator Exam?
This exam is suitable for candidates who want to validate their ability to manage and support the Netskope platform. It is a strong fit for professionals working with cloud security operations and administration.
3. Is the NSK101 exam difficult?
The difficulty depends on your familiarity with cloud security concepts and the Netskope platform. Candidates with practical knowledge of administration, monitoring, and maintenance usually find it easier to prepare effectively.
4. Can I pass NSK101 with only braindumps?
Using dumps alone is not the best approach. You should combine the Exam PDF and Practice Test with a solid review of the exam topics so you understand the concepts and can apply them confidently.
5. Do I need hands-on experience with Netskope?
Hands-on exposure is very helpful because the exam covers management, monitoring, and maintenance tasks. Even if you are using study materials, practical familiarity improves your understanding and confidence.
6. How do QA4Exam.com dumps and practice tests help me pass on the first attempt?
They give you real exam-style questions, verified answers, and a practice environment that mirrors the actual test. This helps you identify weak areas, improve speed, and prepare more effectively for a first-attempt pass.
7. What formats are available for QA4Exam.com NSK101 preparation?
QA4Exam.com provides an Exam PDF with actual questions and answers and an Online Practice Test. Together, they offer convenient review, realistic simulation, and repeated practice for better exam readiness.
The questions for NSK101 were last updated on Jun 4, 2026.
- Viewing page 1 out of 26 pages.
- Viewing questions 1-5 out of 129 questions
Which Netskope component would an administrator use to see an overview of private application usage and performance?
An administrator would use the Digital Experience Management (DEM) component to see an overview of private application usage and performance. DEM provides comprehensive insights into the performance and user experience of private applications, including metrics on latency, bandwidth, and application health.
Digital Experience Management (DEM): This component focuses on monitoring and optimizing the user experience for private and public applications by collecting detailed performance data and providing actionable insights.
The other options do not provide the same level of detailed performance and usage overview for private applications:
Publishers page: Typically used for managing and configuring Netskope Publishers.
Incident Management: Focuses on tracking and resolving security incidents.
Cloud Exchange: Deals with integrations and data sharing between Netskope and other security solutions.
Netskope documentation on Digital Experience Management and its capabilities.
Best practices for using DEM to monitor application performance and enhance user experience.
You want to take into account some recent adjustments to CCI scoring that were made in your Netskope tenant.
In this scenario, which two CCI aspects in the Ul would be used in a real-time protection policy? (Choose two.)
Click the Exhibit button.
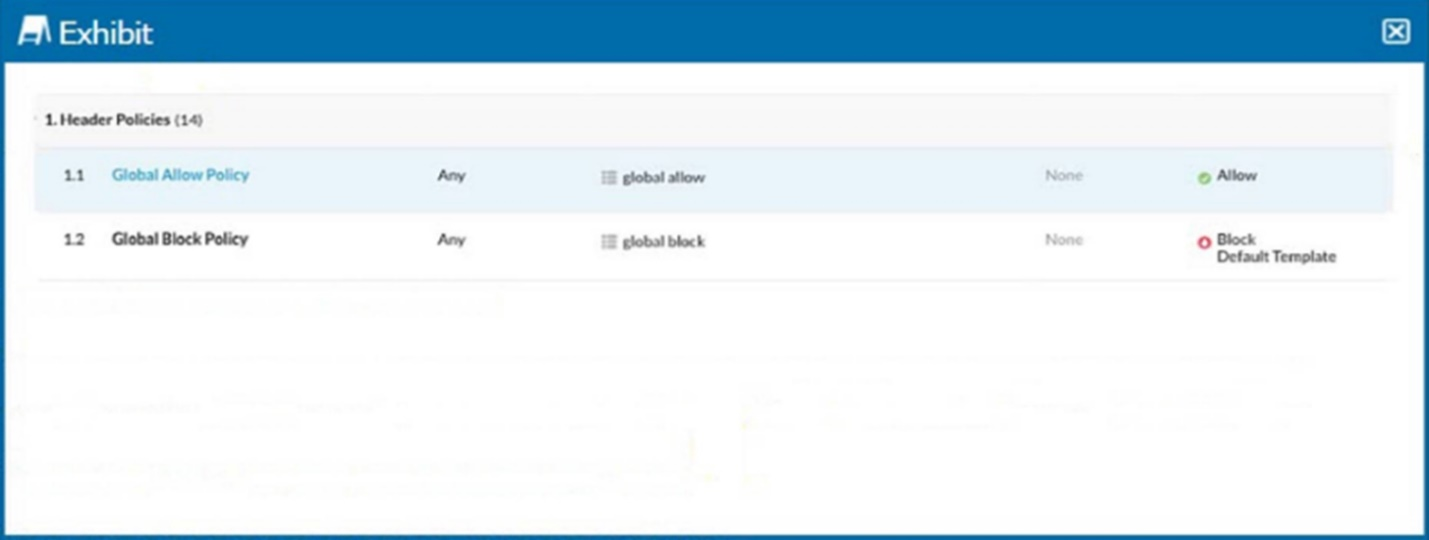
Referring to the exhibit, you have a user reporting that a blocked website is needed for legitimate business reasons. Upon review, you determine that the user has been blocked by the Global Block policy. You need to create an exception forthat domain. You create a custom URL list that includes the domain.
In this scenario, which two actions would allow this access? (Choose two.)
Identify the Blocked Policy: According to the exhibit, the website is blocked by the 'Global Block Policy.'
Create a Custom URL List: To create an exception for the domain, you need to first create a custom URL list that includes the domain in question.
Navigate to the URL List section in the Netskope UI.
Create a new URL list and add the domain that needs to be allowed.
Option B: Create a custom category with the custom URL list as an included URL list and add it to an allow policy above the Global Block policy.
Go to the Policy section in the Netskope UI.
Create a new policy, ensuring it is an 'Allow' policy.
Add the custom category to this allow policy.
Position this allow policy above the Global Block policy to ensure it takes precedence.
This ensures that the URLs in the custom list are allowed before the Global Block policy is evaluated.
Option C: Add the custom URL list as an excluded URL list to the category in the Global Block policy.
Edit the existing Global Block policy.
Add the custom URL list to the excluded URL list section of this policy.
This will exclude the URLs in the custom list from being blocked by the Global Block policy.
Refer to the Netskope Knowledge Portal for managing custom URL lists and policy configurations.
Your department is asked to report on GDPR data publicly exposed in Microsoft 365, Salesforce. and Slack-sanctioned cloud applications. Which deployment model would you use to discover this data?
To discover GDPR data publicly exposed in Microsoft 365, Salesforce, and Slack-sanctioned cloud applications, you need to use a deployment model that allows Netskope to access and scan the data stored in these applications using out-of-band API connections. The deployment model that would match this requirement is API-enabled protection, which is a feature in the Netskope platform that allows you to connect your sanctioned cloud applications to Netskope using API connectors. This enables you to discover sensitive data, enforce near real-time policy controls, and quarantine malware in your cloud applications without affecting user experience or performance. You can use Netskope's data loss prevention (DLP) engine to scan for GDPR data in your cloud applications and identify any public exposure or sharing settings that may violate the regulation. A reverse proxy, an on-premises appliance, or an inline protection are not deployment models that would help you discover GDPR data publicly exposed in your sanctioned cloud applications, as they are more suitable for inline modes that rely on intercepting traffic to and from these applications in real time, rather than accessing data stored in these applications using APIs.Reference:[Netskope SaaS API-enabled Protection], [Netskope Data Loss Prevention].
Which two technologies form a part of Netskope's Threat Protection module? (Choose two.)
Unlock All Questions for Netskope NSK101 Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 129 Questions & Answers