Most Recent Palo Alto Networks NetSec-Generalist Exam Dumps
Prepare for the Palo Alto Networks Network Security Generalist exam with our extensive collection of questions and answers. These practice Q&A are updated according to the latest syllabus, providing you with the tools needed to review and test your knowledge.
QA4Exam focus on the latest syllabus and exam objectives, our practice Q&A are designed to help you identify key topics and solidify your understanding. By focusing on the core curriculum, These Questions & Answers helps you cover all the essential topics, ensuring you're well-prepared for every section of the exam. Each question comes with a detailed explanation, offering valuable insights and helping you to learn from your mistakes. Whether you're looking to assess your progress or dive deeper into complex topics, our updated Q&A will provide the support you need to confidently approach the Palo Alto Networks NetSec-Generalist exam and achieve success.
The questions for NetSec-Generalist were last updated on Jun 3, 2026.
- Viewing page 1 out of 12 pages.
- Viewing questions 1-5 out of 60 questions
Based on the image below, which source IP address will be seen in the data filtering logs of the Cloud NGFW for AWS with the default rulestack settings?
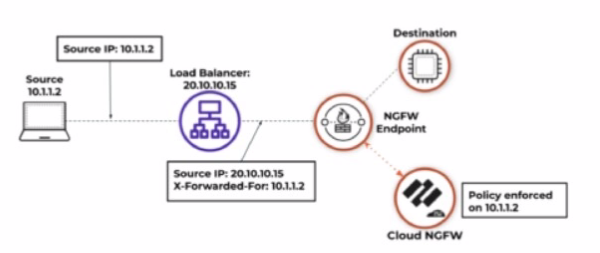
Based on the image and default rulestack settings of the Cloud NGFW for AWS, the source IP address seen in the data filtering logs will be 20.10.10.15, which is the IP address of the load balancer.
Default Rulestack Behavior: By default, the rulestack settings do not inspect or preserve the original client IP (e.g., 10.1.1.2) in the 'X-Forwarded-For' header. Instead, the load balancer's IP (20.10.10.15) is recorded as the source IP.
Logging Mechanism: Unless explicitly configured to parse the 'X-Forwarded-For' header, the firewall's logs will reflect the IP address of the device directly sending the traffic to the NGFW (the load balancer in this case).
Cloud NGFW for AWS Documentation
Data Filtering Logs and Source IP Behavior
When a user works primarily from a remote location but reports to the corporate office several times a month, what does GlobalProtect use to determine if the user should connect to an internal gateway?
GlobalProtect is Palo Alto Networks' VPN and Zero Trust remote access solution. It dynamically determines whether a user should connect to an internal or external gateway based on external host detection.
How External Host Detection Works:
Preconfigured External Host Detection --
The GlobalProtect agent checks for a predefined trusted external IP address (e.g., the corporate office's public IP).
Decision Making --
If the detected IP matches the trusted external host, the GlobalProtect client assumes the user is inside the corporate network and does not establish a VPN connection.
If the detected IP does not match, GlobalProtect initiates a VPN connection to an external gateway.
Improves Performance & Security --
Prevents unnecessary VPN connections when users are inside the corporate office.
Reduces bandwidth overhead by ensuring only external users connect via VPN.
Why Other Options Are Incorrect?
A . ICMP ping to Panorama management interface.
Incorrect, because GlobalProtect does not use ICMP pings to determine location.
Panorama does not play a role in dynamic gateway selection for GlobalProtect.
B . User login credentials.
Incorrect, because credentials are used for authentication, not for detecting location.
Users authenticate regardless of whether they are inside or outside the network.
D . Reverse DNS lookup of preconfigured host IP.
Incorrect, because Reverse DNS lookups are not used for gateway selection.
DNS lookups can be inconsistent and are not a reliable method for internal/external detection.
Reference to Firewall Deployment and Security Features:
Firewall Deployment -- GlobalProtect works with NGFWs to provide secure remote access.
Security Policies -- Can enforce different security postures based on internal vs. external user location.
VPN Configurations -- Uses dynamic gateway selection to optimize VPN performance.
Threat Prevention -- Protects remote users from phishing, malware, and network-based threats.
WildFire Integration -- Inspects files uploaded/downloaded via VPN for threats.
Zero Trust Architectures -- Enforces Zero Trust Network Access (ZTNA) by verifying user identity and device security before granting access.
Thus, the correct answer is: C. External host detection.
A hospital system allows mobile medical imaging trailers to connect directly to the internal network of its various campuses. The network security team is concerned about this direct connection and wants to begin implementing a Zero Trust approach in the flat network.
Which solution provides cost-effective network segmentation and security enforcement in this scenario?
In a Zero Trust Architecture (ZTA), network segmentation is critical to prevent unauthorized lateral movement within a flat network. Since the hospital system allows mobile medical imaging trailers to connect directly to its internal network, this poses a significant security risk, as these trailers may introduce malware, vulnerabilities, or unauthorized access to sensitive medical data.
The most cost-effective and practical solution in this scenario is:
Creating separate security zones for the imaging trailers.
Applying access control and inspection policies via the hospital's existing core firewalls instead of deploying new hardware.
Implementing strict policy enforcement to ensure that only authorized communication occurs between the trailers and the hospital's network.
Why Separate Zones with Enforcement is the Best Solution?
Network Segmentation for Zero Trust
By placing the medical imaging trailers in their own firewall-enforced zone, they are isolated from the main hospital network.
This reduces attack surface and prevents an infected trailer from spreading malware to critical hospital systems.
Granular security policies ensure only necessary communications occur between zones.
Cost-Effective Approach
Uses existing core firewalls instead of deploying costly additional edge firewalls at every campus.
Reduces complexity by leveraging the current security infrastructure.
Visibility & Security Enforcement
The firewall enforces security policies, such as allowing only medical imaging protocols while blocking unauthorized traffic.
Integration with Threat Prevention and WildFire ensures that malicious files or traffic anomalies are detected.
Logging and monitoring via Panorama helps the security team track and respond to threats effectively.
Other Answer Choices Analysis
(A) Deploy edge firewalls at each campus entry point
This is an expensive approach, requiring multiple hardware firewalls at every hospital location.
While effective, it is not the most cost-efficient solution when existing core firewalls can enforce the necessary segmentation and policies.
(B) Manually inspect large images like holograms and MRIs
This does not align with Zero Trust principles.
Manual inspection is impractical, as it slows down medical workflows.
Threats do not depend on image size; malware can be embedded in small and large files alike.
(D) Configure access control lists (ACLs) on core switches
ACLs are limited in security enforcement, as they operate at Layer 3/4 and do not provide deep inspection (e.g., malware scanning, user authentication, or Zero Trust enforcement).
Firewalls offer application-layer visibility, which ACLs on switches cannot provide.
Switches do not log and analyze threats like firewalls do.
Reference and Justification:
Firewall Deployment -- Firewall-enforced network segmentation is a key practice in Zero Trust.
Security Policies -- Granular policies ensure medical imaging traffic is controlled and monitored.
VPN Configurations -- If remote trailers are involved, secure VPN access can be enforced within the zones.
Threat Prevention & WildFire -- Firewalls can scan imaging files (e.g., DICOM images) for malware.
Panorama -- Centralized visibility into all traffic between hospital zones and trailers.
Zero Trust Architectures -- This solution follows Zero Trust principles by segmenting untrusted devices and enforcing least privilege access.
Thus, Configuring separate zones (C) is the correct answer, as it provides cost-effective segmentation, Zero Trust enforcement, and security visibility using existing firewall infrastructure.
Which action must a firewall administrator take to incorporate custom vulnerability signatures into current Security policies?
To incorporate custom vulnerability signatures into current Security policies, administrators must create custom objects. These objects define the specific signature patterns for vulnerabilities, and they can then be applied to security profiles or policies.
Custom Objects: Allow administrators to define and configure unique vulnerability signatures tailored to the organization's specific needs.
Integration into Security Policies: Once created, these custom objects can be referenced in Security policies to detect and mitigate the specified vulnerabilities effectively.
This approach ensures that custom threats not covered by default threat signatures are adequately addressed, enhancing the firewall's threat prevention capabilities.
Custom Vulnerability Signatures in Palo Alto Networks
Threat Prevention Customization
Which tool will help refine a security rule by specifying the applications it has viewed in past weeks?
The Policy Optimizer tool helps refine security rules by analyzing historical traffic data and identifying the applications observed over past weeks. It is designed to:
Improve Security Policies -- Identifies overly permissive rules and suggests specific application-based security policies.
Enhance Rule Accuracy -- Helps replace port-based rules with App-ID-based security rules, reducing the risk of unintended access.
Use Historical Traffic Data -- Analyzes past network activity to determine which applications should be explicitly allowed or denied.
Simplify Rule Management -- Reduces redundant or outdated policies, leading to more effective firewall rule enforcement.
Why Other Options Are Incorrect?
A . Security Lifecycle Review (SLR)
Incorrect, because SLR provides a high-level security assessment, not a tool for refining specific security rules.
It focuses on identifying security gaps rather than optimizing security policies based on past traffic data.
B . Custom Reporting
Incorrect, because Custom Reporting generates security insights and compliance reports, but does not analyze policy rules.
C . Autonomous Digital Experience Management (ADEM)
Incorrect, because ADEM is designed for network performance monitoring, not firewall rule refinement.
It helps measure end-user digital experiences rather than security policy optimizations.
Reference to Firewall Deployment and Security Features:
Firewall Deployment -- Policy Optimizer improves firewall efficiency and accuracy.
Security Policies -- Refines rules based on actual observed application traffic.
VPN Configurations -- Helps optimize security policies for VPN traffic.
Threat Prevention -- Ensures that unused or unnecessary policies do not create security risks.
WildFire Integration -- Works alongside WildFire threat detection to fine-tune application security rules.
Zero Trust Architectures -- Supports least-privilege access control by defining specific App-ID-based rules.
Thus, the correct answer is: D. Policy Optimizer
Unlock All Questions for Palo Alto Networks NetSec-Generalist Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 60 Questions & Answers