Splunk SPLK-1002 Dumps - Pass the Splunk Core Certified Power User Exam in 2026
The Splunk SPLK-1002 exam is part of the Splunk Core Certified Power User certification and is designed for candidates who want to prove practical skills in working with Splunk searches, fields, correlations, and data models. It is a strong fit for users who already work with Splunk data and want to build deeper confidence in transforming, filtering, and enriching results. This certification matters because it validates the ability to use Splunk more effectively in real operational environments. Passing SPLK-1002 shows that you can apply core power user skills to solve everyday analytics and monitoring tasks.
Exam Topics and Approximate Weightage
| # | Exam Topics | Sub-Topics | Approximate Weightage (%) |
|---|---|---|---|
| 1.0 | Using Transforming Commands for Visualizations | chart command usage, stats-based summaries, aggregation for dashboards | 12% |
| 2.0 | Filtering and Formatting Results | search filtering, field formatting, result refinement, output presentation | 10% |
| 3.0 | Correlating Events | event matching, relationship analysis, search correlation, timeline review | 12% |
| 4.0 | Creating and Managing Fields | field extraction, field handling, field visibility, data interpretation | 11% |
| 5.0 | Creating Field Aliases and Calculated Fields | alias creation, calculated field usage, data normalization, search enrichment | 10% |
| 6.0 | Creating Tags and Event Types | tag assignment, event type creation, categorization, search organization | 9% |
| 7.0 | Creating and Using Macros | macro definition, reusable search logic, search simplification, parameter use | 8% |
| 8.0 | Creating and Using Workflow Actions | action configuration, workflow navigation, event interaction, operational shortcuts | 8% |
| 9.0 | Creating Data Models | data model structure, dataset organization, accelerated analytics, model usage | 10% |
| 10.0 | Using the Common Information Model (CIM) Add-On | CIM concepts, add-on usage, normalized data, content alignment | 10% |
This exam tests more than memorization. Candidates need practical knowledge of Splunk search behavior, field management, data enrichment, and content organization, along with the ability to apply these skills in real scenarios. A strong understanding of how Splunk structures and transforms data is essential for success.
How QA4Exam.com Helps You Pass
QA4Exam.com provides an Exam PDF with actual questions and answers plus an Online Practice Test that mirrors the SPLK-1002 exam style. This helps you study with up-to-date questions, verified answers, and a format that feels close to the real test. The practice test also supports time management practice so you can work through questions more efficiently under exam pressure. With both formats, you can review concepts, check your readiness, and build confidence for a first-attempt pass.
Frequently Asked Questions
Who should take the Splunk SPLK-1002 exam?
It is intended for candidates pursuing the Splunk Core Certified Power User certification and for users who want to validate practical Splunk skills.
Is SPLK-1002 considered difficult?
It can be challenging if you do not regularly use Splunk features such as searches, fields, correlations, and data models. Hands-on familiarity helps a lot.
Can I pass SPLK-1002 with only braindumps?
Braindumps alone are not the best approach. You should use them with practice and review so you understand the concepts behind the answers.
Do I need hands-on experience with Splunk?
Yes, hands-on experience is strongly recommended because the exam focuses on applied knowledge and practical usage of Splunk capabilities.
Are QA4Exam.com dumps enough to prepare for the exam?
The Exam PDF and Online Practice Test are very helpful, but the best results come from combining them with review and practical understanding of the listed topics.
How do the QA4Exam.com practice test and PDF help with first-attempt success?
They help you study verified questions and answers, practice under timed conditions, and become familiar with the exam style so you can reduce surprises on test day.
What format do the QA4Exam.com materials come in?
QA4Exam.com offers an Exam PDF and an Online Practice Test for SPLK-1002, giving you both review-friendly study material and a simulated test experience.
The questions for SPLK-1002 were last updated on Jun 3, 2026.
- Viewing page 1 out of 59 pages.
- Viewing questions 1-5 out of 297 questions
Why would the following search produce multiple transactions instead of one?
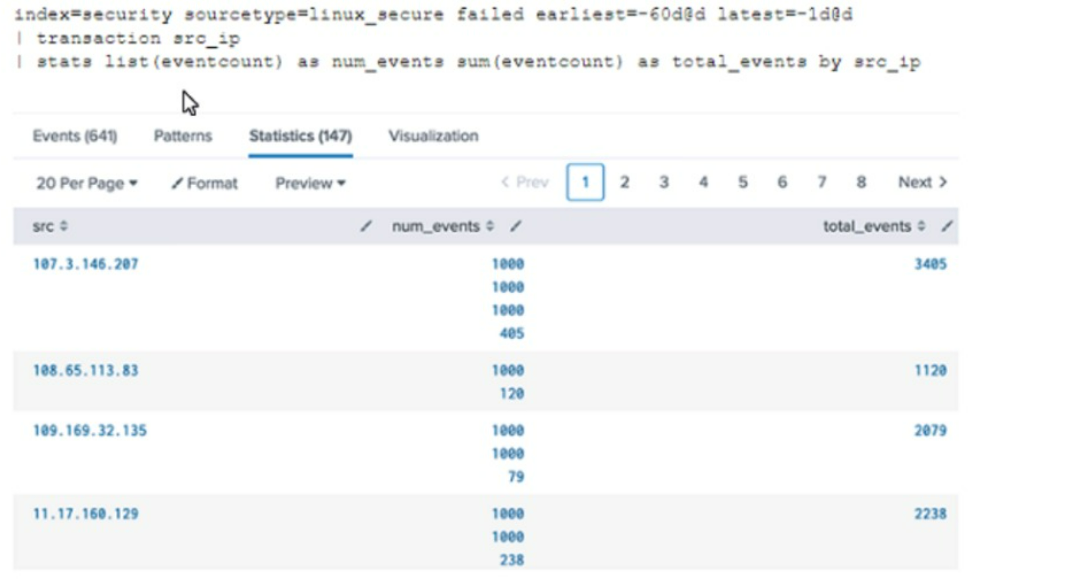
Here is an example of how you can use the maxspan option in a search:
index=main sourcetype=access_combined | transaction someuniqefield maxspan=1h
What is needed to define a calculated field?
A calculated field in Splunk is created using an eval expression, which allows users to perform calculations or transformations on field values during search time.
Splunk Docs - Calculated fields
How is a Search Workflow Action configured to run at the same time range as the original search?
To configure a Search Workflow Action to run at the same time range as the original search, you need to select the ''Use the same time range as the search that created the field listing'' checkbox. This will ensure that the workflow action search uses the same earliest and latest time parameters as the original search.
Which of the following knowledge objects can reference field aliases?
Field aliases in Splunk are alternate names assigned to fields. These can be particularly useful for normalizing data from different sources or simply for making field names more intuitive. Once an alias is created for a field, it can be used across various Splunk knowledge objects, enhancing their flexibility and utility.
A . Calculated fields, lookups, event types, and tags: This is the correct answer. Field aliases can indeed be referenced in calculated fields, lookups, event types, and tags within Splunk. When you create an alias for a field, that alias can then be used in these knowledge objects just like any standard field name.
Calculated fields: These are expressions that can create new field values based on existing data. You can use an alias in a calculated field expression to refer to the original field.
Lookups: These are used to enrich your event data by referencing external data sources. If you've created an alias for a field that matches a field in your lookup table, you can use that alias in your lookup configurations.
Event types: These are classifications for events that meet certain search criteria. You can use field aliases in the search criteria for defining an event type.
Tags: These allow you to assign meaningful labels to data, making it easier to search and report on. You can use field aliases in the search criteria that you tag.
Unlock All Questions for Splunk SPLK-1002 Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 297 Questions & Answers