Most Recent Workday-Pro-Integrations Exam Dumps
Prepare for the Workday Pro Integrations Certification Exam exam with our extensive collection of questions and answers. These practice Q&A are updated according to the latest syllabus, providing you with the tools needed to review and test your knowledge.
QA4Exam focus on the latest syllabus and exam objectives, our practice Q&A are designed to help you identify key topics and solidify your understanding. By focusing on the core curriculum, These Questions & Answers helps you cover all the essential topics, ensuring you're well-prepared for every section of the exam. Each question comes with a detailed explanation, offering valuable insights and helping you to learn from your mistakes. Whether you're looking to assess your progress or dive deeper into complex topics, our updated Q&A will provide the support you need to confidently approach the Workday-Pro-Integrations exam and achieve success.
The questions for Workday-Pro-Integrations were last updated on May 2, 2026.
- Viewing page 1 out of 15 pages.
- Viewing questions 1-5 out of 77 questions
Refer to the following XML to answer the question below.
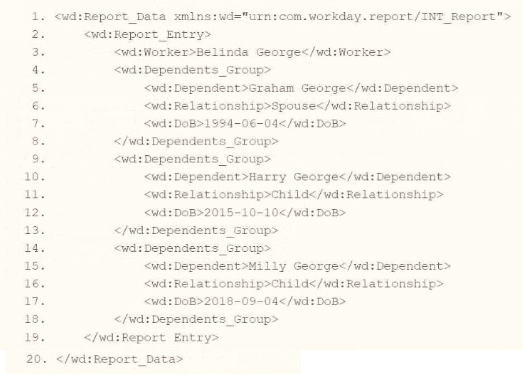
You are an integration developer and need to write XSLT to transform the output of an EIB which is using a web service enabled report to output worker data along with their dependents. You currently have a template which matches on wd:Dependents_Group to iterate over each dependent. Within the template which matches on wd:Dependents_Group you would like to output a relationship code by using an
What XSLT syntax would be used to output SP when the dependent relationship is spouse, output CH when the dependent relationship is child, otherwise output OTHER?
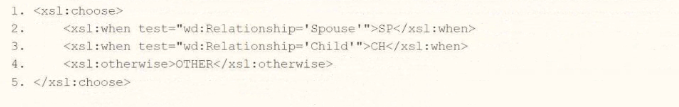
A.
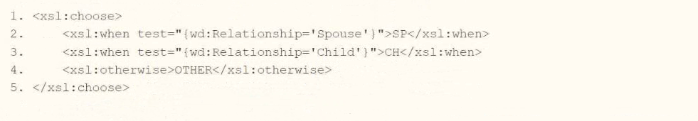
B.
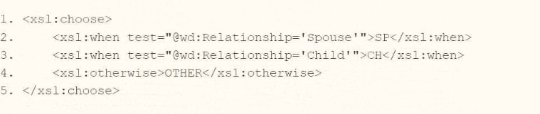
C.
D.
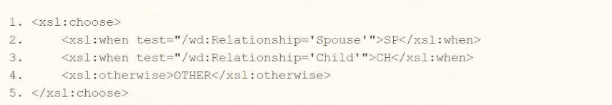
In Workday integrations, XSLT is used to transform XML data, such as the output from an Enterprise Interface Builder (EIB) or a web service-enabled report, into a desired format for third-party systems. In this scenario, you need to write XSLT to process wd:Dependents_Group elements and output a relationship code based on the value of the wd:Relationship attribute or element. The requirement is to output 'SP' for a 'Spouse' relationship, 'CH' for a 'Child' relationship, and 'OTHER' for any other relationship, using an <xsl:choose> statement within a template matching wd:Dependents_Group.
Here's why option C is correct:
XSLT <xsl:choose> Structure: The <xsl:choose> element in XSLT provides conditional logic similar to a switch statement. It evaluates conditions in <xsl:when> elements sequentially, executing the first matching condition, and uses <xsl:otherwise> for any case that doesn't match.
Relationship as an Attribute: Based on the provided XML snippet, wd:Relationship is an attribute (e.g., <wd:Relationship>Spouse</wd:Relationship> within wd:Dependents_Group). However, in Workday XML for integrations, wd:Relationship is often represented as an attribute (@wd:Relationship) rather than a child element, especially in contexts like dependent data in reports. The syntax @wd:Relationship in the test attribute of <xsl:when> correctly references this attribute, aligning with Workday's typical XML structure for such data.
Condition Matching:
The first <xsl:when test='@wd:Relationship='Spouse''>SP</xsl:when> checks if the wd:Relationship attribute equals 'Spouse' and outputs 'SP' if true.
The second <xsl:when test='@wd:Relationship='Child''>CH</xsl:when> checks if the wd:Relationship attribute equals 'Child' and outputs 'CH' if true.
The <xsl:otherwise>OTHER</xsl:otherwise> handles all other cases, outputting 'OTHER' if the relationship is neither 'Spouse' nor 'Child.'
Context in Template: Since the template matches on wd:Dependents_Group, the test conditions operate on the current wd:Dependents_Group element and its attributes, ensuring the correct relationship code is output for each dependent. The XML snippet shows wd:Relationship as an element, but Workday documentation and integration practices often standardize it as an attribute in XSLT transformations, making @wd:Relationship appropriate.
Why not the other options?
A .
xml
WrapCopy
<xsl:choose>
<xsl:when test='wd:Relationship='Spouse''>SP</xsl:when>
<xsl:when test='wd:Relationship='Child''>CH</xsl:when>
<xsl:otherwise>OTHER</xsl:otherwise>
</xsl:choose>
This assumes wd:Relationship is a child element of wd:Dependents_Group, not an attribute. The XML snippet shows wd:Relationship as an element, but in Workday integrations, XSLT often expects attributes for efficiency and consistency, especially in report outputs. Using wd:Relationship without @ would not match the attribute-based structure commonly used, making it incorrect for this context.
B .
xml
WrapCopy
<xsl:choose>
<xsl:when test='@wd:Relationship='Spouse''>SP</xsl:when>
<xsl:when test='@wd:Relationship='Child''>CH</xsl:when>
<xsl:otherwise>OTHER</xsl:otherwise>
</xsl:choose>
This correctly uses @wd:Relationship for an attribute but has a logical flaw: if wd:Relationship='Child', the second <xsl:when> would output 'CH,' but the order of conditions matters. However, the primary issue is that it doesn't match the exact structure or intent as clearly as option C, and Workday documentation often specifies exact attribute-based conditions like those in option C.
D .
xml
WrapCopy
<xsl:choose>
<xsl:when test='/wd:Relationship='Spouse''>SP</xsl:when>
<xsl:when test='/wd:Relationship='Child''>CH</xsl:when>
<xsl:otherwise>OTHER</xsl:otherwise>
</xsl:choose>
This uses an absolute path (/wd:Relationship), which searches for a wd:Relationship element at the root of the XML document, not within the current wd:Dependents_Group context. This would not work correctly for processing dependents in the context of the template matching wd:Dependents_Group, making it incorrect.
To implement this in XSLT:
Within your template matching wd:Dependents_Group, you would include the <xsl:choose> statement from option C to evaluate the wd:Relationship attribute and output the appropriate relationship code ('SP,' 'CH,' or 'OTHER') based on its value. This ensures the transformation aligns with Workday's XML structure and integration requirements for processing dependent data in an EIB or web service-enabled report, even though the provided XML shows wd:Relationship as an element---XSLT transformations often normalize to attributes for consistency.
:
Workday Pro Integrations Study Guide: Section on 'XSLT Transformations for Workday Integrations' -- Details the use of <xsl:choose>, <xsl:when>, <xsl:otherwise>, and XPath for conditional logic in XSLT, including handling attributes like @wd:Relationship.
Workday EIB and Web Services Guide: Chapter on 'XML and XSLT for Report Data' -- Explains the structure of Workday XML (e.g., wd:Dependents_Group, @wd:Relationship) and how to use XSLT to transform dependent data, including attribute-based conditions.
Workday Reporting and Analytics Guide: Section on 'Web Service-Enabled Reports' -- Covers integrating report outputs with XSLT for transformations, including examples of conditional logic for relationship codes.
Refer to the following scenario to answer the question below. You have configured a Core Connector: Worker integration, which utilizes the following basic configuration:
* Integration field attributes are configured to output the Position Title and Business Title fields from the Position Data section.
* Integration Population Eligibility uses the field Is Manager which returns true if the worker holds a manager role.
* Transaction Log service has been configured to Subscribe to specific Transaction Types: Position Edit Event. You launch your integration with the following date launch parameters (Date format of MM/DD/YYYY):
* As of Entry Moment: 05/25/2024 12:00:00 AM
* Effective Date: 05/25/2024
* Last Successful As of Entry Moment: 05/23/2024 12:00:00 AM
* Last Successful Effective Date: 05/23/2024
To test your integration, you made a change to a worker named Jared Ellis who is assigned to the manager role for the IT Help Desk department. You perform an Edit Position on Jared and update their business title to a new value. Jared Ellis' worker history shows the Edit Position Event as being successfully completed with an effective date of 05/27/2024 and an Entry Moment of 05/24/2024 07:58:53 AM however Jared Ellis does not show up in your output. What configuration element would have to be modified for the integration to include Jared Ellis in the output?
The scenario describes a Core Connector: Worker integration configured to output Position Title and Business Title fields for workers who meet the Integration Population Eligibility criteria (Is Manager = true), with the Transaction Log service subscribed to the 'Position Edit Event.' The integration is launched with specific date parameters, and a test is performed by updating Jared Ellis' Business Title via an 'Edit Position' action. Jared is a manager, and the change is logged with an effective date of 05/27/2024 and an entry moment of 05/24/2024 07:58:53 AM. Despite this, Jared does not appear in the output. Let's analyze why and determine the configuration element that needs modification.
In Workday, the Core Connector: Worker integration relies on the Transaction Log service to detect changes based on subscribed transaction types and processes them according to the date launch parameters. The integration is configured as an incremental run (since 'Last Successful' parameters are provided), meaning it captures changes that occurred since the last successful run, within the specified date ranges. The date launch parameters are:
As of Entry Moment: 05/25/2024 12:00:00 AM -- The latest point for when changes were entered into the system.
Effective Date: 05/25/2024 -- The latest effective date for changes to be considered.
Last Successful As of Entry Moment: 05/23/2024 12:00:00 AM -- The starting point for entry moments from the last run.
Last Successful Effective Date: 05/23/2024 -- The starting point for effective dates from the last run.
For an incremental run, Workday processes changes where:
The Entry Moment falls between the Last Successful As of Entry Moment (05/23/2024 12:00:00 AM) and the As of Entry Moment (05/25/2024 12:00:00 AM), and
The Effective Date falls between the Last Successful Effective Date (05/23/2024) and the Effective Date (05/25/2024).
Now, let's evaluate Jared Ellis' change:
Entry Moment: 05/24/2024 07:58:53 AM -- This falls within the range of 05/23/2024 12:00:00 AM to 05/25/2024 12:00:00 AM, so the entry timing is captured correctly.
Effective Date: 05/27/2024 -- This is after the Effective Date of 05/25/2024 specified in the launch parameters.
The issue arises with the Effective Date. The integration only processes changes with an effective date between 05/23/2024 (Last Successful Effective Date) and 05/25/2024 (Effective Date). Jared's change, with an effective date of 05/27/2024, falls outside this range. In Workday, the effective date determines when a change takes effect, and incremental integrations rely on this date to filter relevant transactions. Even though the entry moment (when the change was entered) is within the specified window, the effective date being in the future (relative to the integration's Effective Date of 05/25/2024) excludes Jared from the output.
To include Jared Ellis in the output, the Date launch parameters must be modified. Specifically, the Effective Date needs to be adjusted to a date that includes 05/27/2024 (e.g., 05/27/2024 or later). This ensures the integration captures changes effective up to or beyond Jared's edit. Alternatively, if the intent is to process future-dated changes entered within the current window, the integration could be adjusted to consider the entry moment as the primary filter, though this would typically require a different configuration approach (e.g., full file mode or a custom report, not standard incremental behavior).
Let's evaluate the other options:
A . Integration Population Eligibility: Set to 'Is Manager = true,' and Jared is a manager. This filter is correct and does not need modification.
C . Integration Field Attributes: Configured to output Position Title and Business Title, and the change to Business Title is within scope. The field configuration is appropriate.
D . Transaction log subscription: Subscribed to 'Position Edit Event,' which matches the 'Edit Position' action performed on Jared. The subscription type is correct.
The mismatch between the integration's Effective Date (05/25/2024) and Jared's change effective date (05/27/2024) is the reason for exclusion, making B. Date launch parameters the correct answer.
Workday Pro Integrations Study Guide Reference
Workday Integrations Study Guide: Core Connector: Worker -- Section on 'Change Detection' explains how effective dates and entry moments govern incremental processing.
Workday Integrations Study Guide: Launch Parameters -- Details the roles of 'Effective Date' and 'As of Entry Moment' in filtering changes, emphasizing that incremental runs focus on the effective date range.
Workday Integrations Study Guide: Incremental Processing -- Describes how future-dated changes (effective dates beyond the launch parameter) are excluded unless the parameters are adjusted accordingly.
You have a population of workers who have put multiple names in their Legal Name - First Name Workday delivered field. Your third-party vendor only accepts one-word first names. For workers that have included a middle name, the first and middle names are separated by a single space. You have been asked to implement the following logic:
* Extract the value before the single space from the Legal Name - First Name Workday delivered field.
* Count the number of characters in the extracted value.
* Identify if the number of characters is greater than.
* If the count of characters is greater than 0, use the extracted value. Otherwise, use the Legal Name - First Name Workday delivered field.
What functions are needed to achieve the end goal?
The task involves processing the 'Legal Name - First Name' field in Workday to meet a third-party vendor's requirement of accepting only one-word first names. For workers with multiple names (e.g., 'John Paul'), separated by a single space, the logic must:
Extract the value before the space (e.g., 'John' from 'John Paul').
Count the characters in the extracted value.
Check if the character count is greater than 0.
Use the extracted value if the count is greater than 0; otherwise, use the original 'Legal Name - First Name' field.
This logic is typically implemented in Workday using calculated fields within a custom report or integration (e.g., EIB or Studio). Let's break down the required functions:
Substring Text:This function is needed to extract the portion of the 'Legal Name - First Name' field before the space. In Workday, the Substring Text function allows you to specify a starting position (e.g., 1) and extract text up to a delimiter (e.g., a space). For example, Substring Text('John Paul', 1, Index of ' ') would return 'John.'
Text Length:After extracting the substring (e.g., 'John'), the logic requires counting its characters to ensure it's valid. The Text Length function returns the number of characters in a text string (e.g., Text Length('John') = 4). This is critical for the condition check.
True/False Condition:The logic involves a conditional check: 'Is the number of characters greater than 0?' The True/False Condition function evaluates this (e.g., Text Length(extracted value) > 0), returning True if the extracted value exists and False if it's empty (e.g., if no space exists or extraction fails).
Evaluate Expression:This function implements the if-then-else logic: if the character count is greater than 0, use the extracted value (e.g., 'John'); otherwise, use the original 'Legal Name - First Name' field (e.g., 'John Paul'). Evaluate Expression combines the True/False Condition with the output values.
Option Analysis:
A . Extract Single Instance, Text Length, Numeric Constant, True/False Condition: Incorrect. Extract Single Instance is used for multi-instance fields (e.g., selecting one dependent), not text parsing. Numeric Constant isn't needed here, as no fixed number is involved.
B . Text Constant, Substring Text, Arithmetic Calculation, Evaluate Expression: Incorrect. Text Constant provides a fixed string (e.g., 'abc'), not dynamic extraction. Arithmetic Calculation isn't required, as this is a text length check, not a numeric operation beyond comparison.
C . Format Text, Convert Text to Number, True/False Condition, Evaluate Expression: Incorrect. Format Text adjusts text appearance (e.g., capitalization), not extraction. Convert Text to Number isn't needed, as Text Length already returns a number.
D . Substring Text, Text Length, True/False Condition, Evaluate Expression: Correct. These functions align perfectly with the requirements: extract the first name, count its length, check the condition, and choose the output.
Implementation:
Create a calculated field using Substring Text to extract text before the space.
Use Text Length to count characters in the extracted value.
Use True/False Condition to check if the length > 0.
Use Evaluate Expression to return the extracted value or the original field based on the condition.
Reference from Workday Pro Integrations Study Guide:
Workday Calculated Fields: Section on 'Text Functions' details Substring Text and Text Length usage.
Integration System Fundamentals: Explains how calculated fields with conditions (True/False, Evaluate Expression) transform data for third-party systems.
Core Connectors & Document Transformation: Highlights text manipulation for outbound integration requirements.
Refer to the following XML to answer the question below.
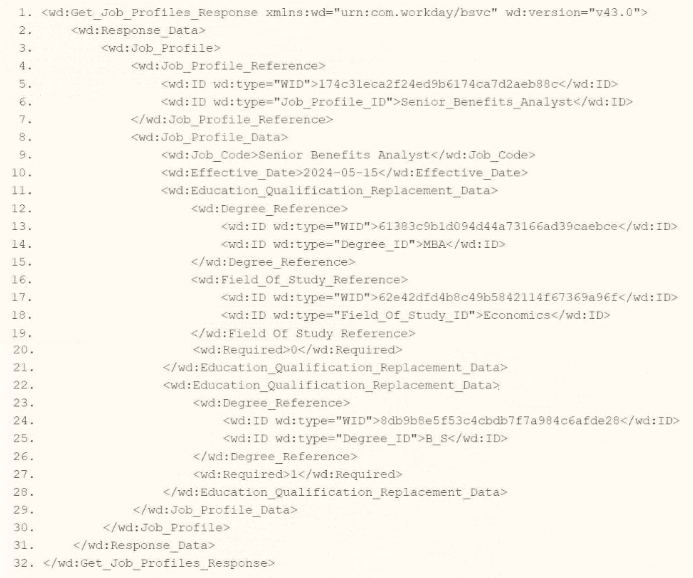
You are an integration developer and need to write XSLT to transform the output of an EIB which is making a request to the Get Job Profiles web service operation. The root template of your XSLT matches on the
As an integration developer working with Workday, you are tasked with transforming the output of an Enterprise Interface Builder (EIB) that calls the Get_Job_Profiles web service operation. The provided XML shows the response from this operation, and you need to write XSLT to select the value of the <wd:ID> element where the wd:type attribute equals 'Job_Profile_ID.' The root template of your XSLT matches on <wd:Get_Job_Profiles_Response> and applies templates to <wd:Job_Profile>. Within this template, you use the <xsl:value-of> element to extract the value. Let's analyze the XML structure, the requirement, and each option to determine the correct XPath syntax.
Understanding the XML and Requirement
The XML snippet provided is a SOAP response from the Get_Job_Profiles web service operation in Workday, using the namespace xmlns:wd='urn:com.workday/bsvc' and version wd:version='v43.0'. Key elements relevant to the question include:
The root element is <wd:Get_Job_Profiles_Response>.
It contains <wd:Response_Data>, which includes <wd:Job_Profile> elements.
Within <wd:Job_Profile>, there is <wd:Job_Profile_Reference>, which contains multiple <wd:ID> elements, each with a wd:type attribute:
<wd:ID wd:type='WID'>1740d3eca2f2ed9b6174ca7d2ae88c8c</wd:ID>
<wd:ID wd:type='Job_Profile_ID'>Senior_Benefits_Analyst</wd:ID>
The task is to select the value of the <wd:ID> element where wd:type='Job_Profile_ID' (e.g., 'Senior_Benefits_Analyst') using XPath within an XSLT template that matches <wd:Job_Profile>. The <xsl:value-of> element outputs the value of the selected node, so you need the correct XPath path from the <wd:Job_Profile> context to the specific <wd:ID> element with the wd:type attribute value 'Job_Profile_ID.'
Analysis of Options
Let's evaluate each option based on the XML structure and XPath syntax rules:
Option A: wd:Job_Profile_Reference/wd:ID/wd:type='Job_Profile_ID'
This XPath attempts to navigate from wd:Job_Profile_Reference to wd:ID, then to wd:type='Job_Profile_ID'. However, there are several issues:
wd:type='Job_Profile_ID' is not valid XPath syntax. In XPath, to filter based on an attribute value, you use the attribute selector [@attribute='value'], not a direct comparison like wd:type='Job_Profile_ID'.
wd:type is an attribute of <wd:ID>, not a child element or node. This syntax would not select the <wd:ID> element itself but would be interpreted as trying to match a nonexistent child node or property, resulting in an error or no match.
This option is incorrect because it misuses XPath syntax for attribute filtering.
Option B: wd:Job_Profile_Reference/wd:ID/@wd:type='Job_Profile_ID'
This XPath navigates to wd:Job_Profile_Reference/wd:ID and then selects the @wd:type attribute, comparing it to 'Job_Profile_ID' with =@wd:type='Job_Profile_ID'. However:
The =@wd:type='Job_Profile_ID' syntax is invalid in XPath. To filter based on an attribute value, you use [@wd:type='Job_Profile_ID'] as a predicate, not an equality comparison in this form.
This XPath would select the wd:type attribute itself (e.g., the string 'Job_Profile_ID'), not the value of the <wd:ID> element. Since <xsl:value-of> expects a node or element value, selecting an attribute directly would not yield the desired 'Senior_Benefits_Analyst' value.
This option is incorrect due to the invalid syntax and inappropriate selection of the attribute instead of the element value.
Option C: wd:Job_Profile_Reference/wd:ID[@wd:type='Job_Profile_ID']
This XPath navigates from wd:Job_Profile_Reference to wd:ID and uses the predicate [@wd:type='Job_Profile_ID'] to filter for <wd:ID> elements where the wd:type attribute equals 'Job_Profile_ID.'
In the XML, <wd:Job_Profile_Reference> contains:
<wd:ID wd:type='WID'>1740d3eca2f2ed9b6174ca7d2ae88c8c</wd:ID>
<wd:ID wd:type='Job_Profile_ID'>Senior_Benefits_Analyst</wd:ID>
The predicate [@wd:type='Job_Profile_ID'] selects the second <wd:ID> element, whose value is 'Senior_Benefits_Analyst.'
Since the template matches <wd:Job_Profile>, and <wd:Job_Profile_Reference> is a direct child of <wd:Job_Profile>, this path is correct:
<wd:Job_Profile> <wd:Job_Profile_Reference> <wd:ID[@wd:type='Job_Profile_ID']>.
When used with <xsl:value-of select='wd:Job_Profile_Reference/wd:ID[@wd:type='Job_Profile_ID']'/>, it outputs 'Senior_Benefits_Analyst,' fulfilling the requirement.
This option is correct because it uses proper XPath syntax for attribute-based filtering and selects the desired <wd:ID> value.
Option D: wd:Job_Profile_Reference/wd:ID/[@wd:type='Job_Profile_ID']
This XPath is similar to Option C but includes an extra forward slash before the predicate: wd:ID/[@wd:type='Job_Profile_ID']. In XPath, predicates like [@attribute='value'] are used directly after the node name (e.g., wd:ID[@wd:type='Job_Profile_ID']), not separated by a slash. The extra slash is syntactically incorrect and would result in an error or no match, as it implies navigating to a child node that doesn't exist.
This option is incorrect due to the invalid syntax.
Why Option C is Correct
Option C, wd:Job_Profile_Reference/wd:ID[@wd:type='Job_Profile_ID'], is the correct XPath syntax because:
It starts from the context node <wd:Job_Profile> (as the template matches this element) and navigates to <wd:Job_Profile_Reference/wd:ID>, using the predicate [@wd:type='Job_Profile_ID'] to filter for the <wd:ID> element with wd:type='Job_Profile_ID'.
It correctly selects the value 'Senior_Benefits_Analyst,' which is the content of the <wd:ID> element where wd:type='Job_Profile_ID'.
It uses standard XPath syntax for attribute-based filtering, aligning with Workday's XSLT implementation for web service responses.
When used with <xsl:value-of>, it outputs the required value, fulfilling the question's requirement.
Practical Example in XSLT
Here's how this might look in your XSLT:
<xsl:template match='wd:Job_Profile'>
<xsl:value-of select='wd:Job_Profile_Reference/wd:ID[@wd:type='Job_Profile_ID']'/>
</xsl:template>
This would output 'Senior_Benefits_Analyst' for the <wd:ID> element with wd:type='Job_Profile_ID' in the XML.
Verification with Workday Documentation
The Workday Pro Integrations Study Guide and SOAP API Reference (available via Workday Community) detail the structure of the Get_Job_Profiles response and how to use XPath in XSLT for transformations. The XML structure shows <wd:Job_Profile_Reference> containing <wd:ID> elements with wd:type attributes, and the guide emphasizes using predicates like [@wd:type='value'] to filter based on attributes. This is a standard practice for navigating Workday web service responses.
Workday Pro Integrations Study Guide Reference
Section: XSLT Transformations in EIBs -- Describes using XSLT to transform web service responses, including selecting elements with XPath and attribute predicates.
Section: Workday Web Services -- Details the Get_Job_Profiles operation and its XML output structure, including <wd:Job_Profile_Reference> and <wd:ID> with wd:type attributes.
Section: XPath Syntax -- Explains how to use predicates like [@wd:type='Job_Profile_ID'] for attribute-based filtering in Workday XSLT.
Workday Community SOAP API Reference -- Provides examples of XPath navigation for Workday web service responses, including attribute selection.
Option C is the verified answer, as it correctly selects the <wd:ID> value with wd:type='Job_Profile_ID' using the appropriate XPath syntax within the <wd:Job_Profile> template context.
An external system needs a file containing data for recent compensation changes. They would like to receive a file routinely at 5 PM eastern standard time, excluding weekends. The file should show compensation changes since the last integration run.
What is the recurrence type of the integration schedule?
Understanding the Requirement
The question involves scheduling an integration in Workday to deliver a file containing recent compensation changes to an external system. The key requirements are:
The file must be delivered routinely at 5 PM Eastern Standard Time (EST).
The recurrence should exclude weekends (i.e., run only on weekdays: Monday through Friday).
The file should include compensation changes since the last integration run, implying an incremental data pull, though this does not directly affect the recurrence type.
The task is to identify the correct recurrence type for the integration schedule from the given options:
A . Recurs every 12 hours
B . Recurs every weekday
C . Dependent recurrence
D . Recurs every 1 day(s)
Analysis of the Workflow and Recurrence Options
In Workday, integrations are scheduled using the Integration Schedule functionality, typically within tools like Enterprise Interface Builder (EIB) or Workday Studio, though this scenario aligns closely with EIB for routine file-based integrations. The recurrence type determines how frequently and under what conditions the integration runs. Let's evaluate each option against the requirements:
Step-by-Step Breakdown
Time Specification (5 PM EST):
Workday allows scheduling integrations at a specific time of day (e.g., 5 PM EST). This is set in the schedule configuration and is independent of the recurrence type but confirms the need for a daily-based recurrence with a specific time slot.
Exclusion of Weekends:
The requirement explicitly states the integration should not run on weekends (Saturday and Sunday), meaning it should only execute on weekdays (Monday through Friday). This is a critical filter for choosing the recurrence type.
Incremental Data (Since Last Run):
The file must include compensation changes since the last integration run. In Workday, this is typically handled by configuring the integration (e.g., via a data source filter or 'changed since' parameter in EIB), not the recurrence type. Thus, this requirement does not directly influence the recurrence type but confirms the integration runs periodically.
Unlock All Questions for Workday Workday-Pro-Integrations Exam
Full Exam Access, Actual Exam Questions, Validated Answers, Anytime Anywhere, No Download Limits, No Practice Limits
Get All 77 Questions & Answers